TL;DR:
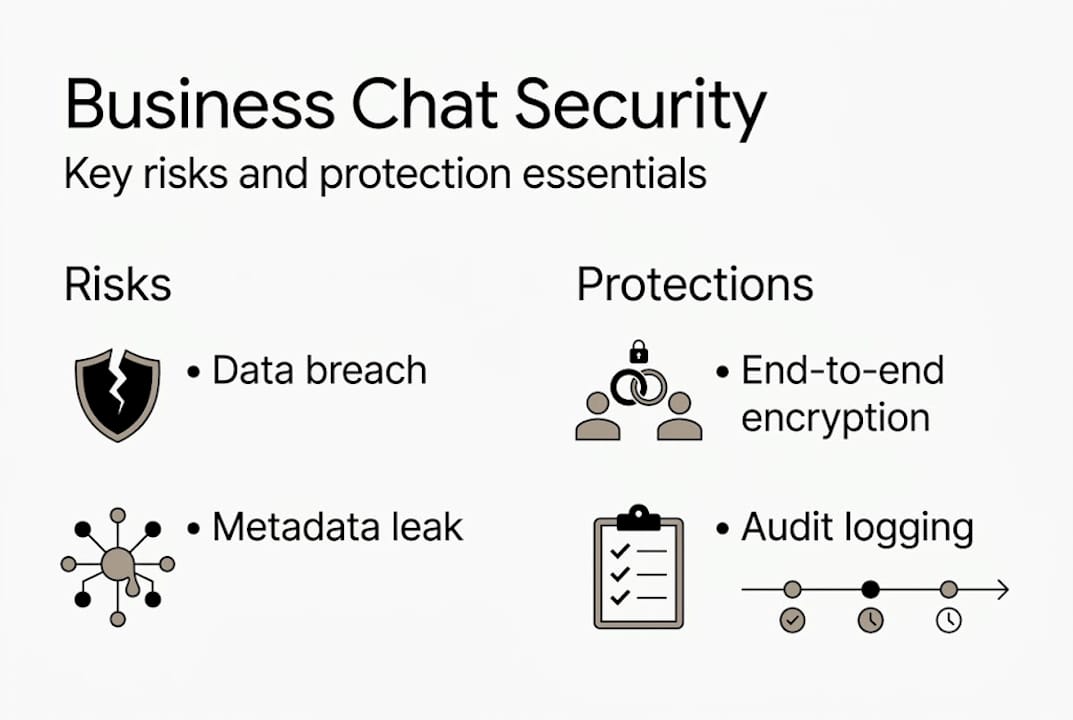
- Many consumer chat apps lack essential enterprise security controls like E2EE and audit logs.
- Secure business chat requires protocols like X3DH, AES-256, and compliance with standards like GDPR and HIPAA.
- AI integration in messaging must balance improved productivity with data privacy and regulatory compliance.
Many IT and communications managers assume that widely adopted chat tools are automatically enterprise-ready. They are not. Consumer apps lack key enterprise security and compliance controls that regulated industries and security-conscious organizations actually need. A data breach traced back to an unvetted messaging tool is not a hypothetical scenario anymore. This article walks you through why secure business chat demands a specialized approach, how the underlying security mechanics work, which platforms lead the field in 2026, and how AI is reshaping what secure collaboration looks like for modern enterprises.
Table of Contents
- Why secure business chat matters for the modern enterprise
- How secure business chat platforms work: Encryption, authentication, and beyond
- Comparing leading secure business chat solutions
- AI-driven collaboration: The new frontier in secure business chat
- Rethinking secure business chat: What most enterprises still miss
- How Luxenger enables truly secure, AI-powered business chat
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| E2EE is essential | End-to-end encryption is critical but must be combined with compliance and admin oversight for enterprise security. |
| Platform choice matters | Not all 'secure chat' apps meet enterprise needs—check for compliance certifications and audit features. |
| AI enhances productivity | AI-driven features can boost collaboration but should be reviewed for compliance before rollout. |
| Don't overlook metadata | Even with E2EE, leaks from metadata or weak key management are real-world risks enterprises must address. |
Why secure business chat matters for the modern enterprise
Let's be direct: unprotected chat is one of the easiest attack surfaces in an enterprise environment. Employees send sensitive project details, financial figures, personnel information, and client data through messaging tools every day. If that tool is not purpose-built for enterprise security, you are accepting risk that most IT and compliance teams would not tolerate in any other system.
The financial stakes are real. Data breaches cost organizations an average of $4.88 million per incident, and communication channels are increasingly targeted by attackers looking for the path of least resistance. When a chat message is intercepted or a misconfigured admin account is exploited, the damage extends well beyond the immediate leak.
For teams operating in finance, healthcare, legal, or government, the stakes climb even higher. GDPR, HIPAA, and SOC 2 compliance requirements apply directly to how your organization handles communication data, and failure to meet them attracts regulatory fines and lasting reputational damage. Your chat platform is not exempt from these obligations.
Three capabilities separate compliant enterprise chat from generic messaging:
- End-to-end encryption (E2EE): Messages must be readable only by sender and recipient, not by the platform provider.
- Audit logs: A verifiable record of who said what, when, and from which device is essential for compliance investigations and incident response.
- Single sign-on (SSO) and access controls: Integration with your identity provider ensures that only authorized personnel access sensitive channels, and that offboarding is immediate and complete.
Without these, your enterprise chat security posture has gaps that auditors, attackers, and regulators will eventually find.
Pro Tip: Never assume a chat tool is compliant just because a vendor uses security-sounding language in their marketing. Verify that specific regulations are covered, and get that confirmation in writing before deployment.
How secure business chat platforms work: Encryption, authentication, and beyond
Understanding the mechanics behind secure chat helps you evaluate vendor claims without getting lost in jargon. Most enterprise-grade platforms use established protocols combined with newer advances to protect messages across their full lifecycle.
Here is how a message travels securely from one employee to another:
- Message creation: The sender's app generates a unique encryption key for that session.
- Key exchange: Using a protocol like X3DH (Extended Triple Diffie-Hellman), both parties establish a shared secret without that secret ever crossing the network in plaintext.
- Encryption: The message is encrypted locally using AES-256 before it leaves the device.
- Transmission: Only the encrypted ciphertext travels through the server. The server cannot read it.
- Decryption: The recipient's device uses the shared key to decrypt the message locally.
- Forward secrecy: Each session generates new keys, so a compromised key does not expose past conversations.
Platforms use protocols like Signal Protocol, MLS (Messaging Layer Security), Double Ratchet, AES-256, and increasingly post-quantum algorithms to future-proof against quantum computing attacks. Post-quantum readiness matters now because adversaries using "harvest now, decrypt later" strategies are already collecting encrypted data with the intent to break it once quantum hardware matures.
"True security requires E2EE combined with minimal metadata exposure and verified keys. Consumer apps like Signal are excellent for individuals but lack the admin controls, audit capabilities, and key management infrastructure that enterprise environments require."
Performance is also a legitimate concern. Empirical latency benchmarks show that modern secure messaging protocols add minimal overhead. Wire achieves key exchange in approximately 89ms on 3G networks, and Signal handles message delivery in around 210ms, making security nearly imperceptible to users.
| Protocol | Encryption standard | Post-quantum ready | Key exchange |
|---|---|---|---|
| Signal Protocol | AES-256, Double Ratchet | Partial | X3DH |
| MLS | AES-256 | In development | TreeKEM |
| Matrix/Element | AES-256, Olm/Megolm | Partial | X3DH |
| Wickr | AES-256 | Yes | Custom |
Exploring the must-have secure messaging features in depth will help you build a technical requirements checklist before you evaluate vendors. You can also map those features to secure workflow steps to ensure your implementation matches your threat model.
Comparing leading secure business chat solutions
Top-rated platforms for 2026 include Wire, Threema Work, Element (Matrix), Amazon Wickr, Mattermost, Microsoft Teams, Slack, Google Chat, and Brosix. Each takes a different approach to the balance between security depth, usability, and compliance coverage.
| Platform | True E2EE | Compliance certs | On-prem option | AI integration |
|---|---|---|---|---|
| Amazon Wickr | Yes | HIPAA, FedRAMP | Yes | Limited |
| Mattermost | Yes | SOC 2, GDPR | Yes | Growing |
| Wire | Yes | GDPR | Yes | Limited |
| Element (Matrix) | Yes | GDPR | Yes | Via plugins |
| Microsoft Teams | No (by default) | HIPAA, SOC 2 | No | Copilot add-on |
| Slack | No (by default) | SOC 2, HIPAA | No | AI included |
| Google Chat | No (by default) | SOC 2, HIPAA | No | Gemini included |
| Threema Work | Yes | GDPR | Yes | No |
A few things stand out from this comparison. Teams, Slack, and Google Chat dominate enterprise adoption, but none offers true E2EE by default. That means message content is technically accessible to the platform provider, which creates exposure for regulated industries and organizations with strict data sovereignty requirements.
Platforms like Wickr and Mattermost close that gap with genuine E2EE and on-premises deployment options, which keep your data within your own infrastructure. The trade-off is typically a steeper implementation cost and more demanding IT management.
Key factors to weigh when selecting a platform:
- E2EE coverage: Does it apply to group chats, file transfers, and video calls, or just one-to-one messages?
- Admin and audit features: Can your team access logs, revoke access, and export records for compliance investigations?
- Identity integration: Does it support SAML, LDAP, or your existing identity provider?
- Deployment model: Cloud-only, hybrid, or full on-premises hosting?
See secure messaging examples from organizations that have navigated this selection process, and consult the guide on choosing a secure platform to structure your evaluation criteria.
Pro Tip: Do not let a feature checklist drive your final decision. A platform that checks every box on paper but does not align with your auditing workflows or employee usage patterns will create adoption problems that undermine your security posture anyway.
AI-driven collaboration: The new frontier in secure business chat
Artificial intelligence is now embedded in the top enterprise messaging platforms, and it is changing how teams consume, organize, and act on communication at scale. For IT and communications managers, the question is no longer whether to adopt AI-enhanced messaging, but how to do it without introducing new compliance exposure.

Slack AI bundles summaries and search directly into enterprise plans, Microsoft Copilot is available as a $30/user/month add-on for Teams, and Google Gemini provides summarization features inside Google Chat. Each approach has different implications for how your data is processed and where it goes.
The productivity case for AI in secure chat is strong. Intelligent summaries let team members catch up on long threads without reading everything. Smart search surfaces relevant conversations across months of history. Automated compliance monitoring flags policy violations before they become incidents.
But every AI feature introduces a data processing question: where is the model running, and who has access to the inputs? Cloud-based AI features that process message content on external servers may conflict with data residency requirements or your E2EE model, because the platform needs access to plaintext content to generate summaries.
Checklist for evaluating AI features in a secure chat platform:
- Does the AI process data on-device, on your private servers, or on the vendor's cloud?
- Is AI processing subject to the same encryption and access controls as your messages?
- Does the vendor provide a data processing agreement that covers AI model training?
- Can you disable AI features for specific channels or user groups?
- Are AI outputs logged and auditable for compliance purposes?
The top AI features for secure chat worth prioritizing are those that enhance usability without requiring the platform to access your unencrypted message content. Review the broader landscape of AI collaboration tools and explore the full guide on AI-powered collaboration to align your evaluation with both security and productivity goals.
Rethinking secure business chat: What most enterprises still miss
Here is the uncomfortable reality: most organizations that invest in a secure chat platform are still underprotected, not because the technology failed, but because they stopped asking hard questions after the initial deployment.
E2EE is necessary but not the whole picture. True security goes beyond E2EE to include minimal metadata exposure, robust key verification, and full auditability. Metadata, including who communicated with whom, when, and for how long, can reveal sensitive organizational patterns even when message content is encrypted. Most enterprise teams never audit their metadata policies.
Admin backdoors are another overlooked risk. Many enterprise platforms give administrators broad access to message content for compliance purposes, which is a legitimate need. But that access also creates an internal threat vector that few organizations control rigorously enough.
The most dangerous gap we see is adoption driven by price or familiarity rather than threat modeling. Teams default to the platform everyone already uses, without questioning whether that platform actually matches their risk profile. Before your next renewal or platform evaluation, challenge your vendors with specific questions about metadata policies, key management, and incident response. Then ask yourself the same questions internally. Understand the real value of messaging platforms in 2026 before committing to a tool just because it is convenient.
How Luxenger enables truly secure, AI-powered business chat
Secure, productive enterprise messaging does not require a trade-off between protection and capability. Luxenger for enterprise delivers bank-grade E2EE alongside AI-powered conversation summaries, real-time multilingual translation, and voice huddles designed for distributed teams.
Luxenger supports SSO integration, detailed audit logging, and on-premises deployment options for organizations with strict data residency requirements. Whether your compliance obligations are driven by HIPAA, GDPR, or SOC 2, the platform is built to meet them. Review Luxenger pricing to see how enterprise security scales with your team, or explore the full Luxenger platform to see AI-enhanced secure communication in action.
Frequently asked questions
Which secure business chat apps have true end-to-end encryption?
Wire, Threema Work, Element (Matrix), Amazon Wickr, and Mattermost offer true end-to-end encryption, while Teams and Slack do not enable it by default.
How do AI tools affect secure business chat compliance?
AI-driven features can improve productivity but may introduce new risks; enterprises should ensure these tools comply with industry regulations before deployment, particularly around where AI processes message data.
What threats remain despite end-to-end encryption?
Metadata leaks and poor key management can still expose sensitive organizational patterns and communication records even when message content itself is encrypted.
Does secure business chat slow down communication?
Modern secure apps are optimized for speed. Wire achieves key exchange in 89ms on 3G networks, and Signal handles messages in around 210ms, making the security overhead nearly invisible to users.
Which compliance standards do secure business chat platforms typically meet?
Top platforms support GDPR, HIPAA, and SOC 2 compliance, which are critical requirements for enterprises operating in regulated industries like healthcare, finance, and legal services.
