Corporate data breaches rarely start with sophisticated hacking. They start with a poorly secured chat thread. 75% of corporate leaks trace back to missing message-layer encryption, meaning the biggest threat to your enterprise may already be inside your communication stack. This guide walks IT and communications managers through every stage of building a secure internal messaging workflow, from assessing risk exposure to continuous improvement, so your teams can collaborate with confidence and your organization stays protected.
Table of Contents
- Assess your enterprise's messaging risks and requirements
- Select protocols and platforms for end-to-end secure messaging
- Integrate compliance, audit, and workflow controls
- Test, monitor, and continuously improve secure workflows
- Advanced secure messaging solutions for enterprise teams
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Start with risk analysis | Identifying vulnerabilities and compliance needs upfront ensures targeted workflow improvements. |
| Prioritize E2EE protocols | Signal or MLS encryption and strong authentication are essential for safe enterprise collaboration. |
| Integrate compliance controls | Built-in retention, eDiscovery, and audit logs help you meet regulatory requirements and reduce breach impacts. |
| Continuous testing matters | Regular verification and benchmarking are key to resilient, secure workflows that adapt to evolving threats. |
| Enterprise platforms streamline solutions | Choosing specialized messaging platforms simplifies secure workflow implementation and ongoing management. |
Assess your enterprise's messaging risks and requirements
Before you redesign any workflow, you need a clear picture of where your messaging environment is exposed. Most enterprises run a mix of tools, some sanctioned, some not, and that fragmentation creates gaps that attackers exploit. 70% of security breaches stem from unsecured messaging channels, which means your risk assessment is not a formality. It is the foundation of everything that follows.

Start with a channel sensitivity assessment. Map every messaging tool in use across departments, including shadow IT apps employees have adopted without IT approval. Pay special attention to BYOD environments, where personal devices access corporate channels without consistent security controls. Mobile access points are among the highest-risk areas in any enterprise messaging setup.
Next, define your compliance requirements. Different industries carry different obligations, and your workflow must account for all of them. Use this checklist to identify what applies to your organization:
- eDiscovery support: Can messages be retrieved and produced in legal proceedings?
- Retention policies: Are messages stored for the required duration and then purged?
- Data residency: Do messages stay within required geographic boundaries?
- Records management: Are audit trails maintained for regulatory review?
- Encryption at rest and in transit: Is message content protected throughout its lifecycle?
Not all messaging tools are built for enterprise-grade compliance. The table below compares common options across key security dimensions:
| Tool type | E2EE support | Admin controls | Compliance features | Audit logs |
|---|---|---|---|---|
| Consumer apps (e.g., WhatsApp) | Partial | Minimal | None | No |
| RCS (Rich Communication Services) | Optional via MLS for scalable group E2EE | Limited | Emerging | Limited |
| Proprietary enterprise platforms | Full | Robust | Comprehensive | Yes |
| Open-source platforms | Varies | Configurable | Requires setup | Configurable |
For a deeper look at how these categories compare in practice, the enterprise secure messaging guide breaks down what each tool type actually delivers. You can also explore types of secure workplace messaging apps to match options to your specific environment.
Pro Tip: Run your channel sensitivity assessment before touching any platform settings. Knowing which conversations carry the highest risk, executive communications, legal discussions, HR matters, tells you exactly where to apply the strictest controls first.
Select protocols and platforms for end-to-end secure messaging
Once you have mapped your needs, the next step is selecting protocols and platforms with the right blend of security and functionality. This is where technical decisions have long-term consequences, so precision matters.
Encryption protocols are the backbone of secure messaging. The three most relevant for enterprise use are:
- Signal Protocol: Best for one-to-one encrypted messaging. Widely regarded as the gold standard for individual conversations.
- MLS (Messaging Layer Security): Designed for scalable group encryption. RFC9750 recommends MLS for group chats, with Signal Protocol for 1:1 messaging, and emphasizes key rotation and post-compromise security.
- RCS (Rich Communication Services): An emerging standard that supports E2EE when properly configured, though enterprise-grade implementation varies by provider.
Understanding end-to-end encryption is essential before committing to any protocol. E2EE ensures that only the sender and recipient can read a message, with no access point in between, not even the platform provider.
Authentication is equally critical. Weak login controls undermine even the strongest encryption. Your platform must support:
- Multi-factor authentication (MFA): Required for all users, not just admins.
- FIDO2 hardware keys: Phishing-resistant authentication for high-privilege accounts.
- Device attestation: Verifying that only approved, compliant devices can access the messaging environment.
Improper cryptography causes 14% of breaches, and Perfect Forward Secrecy (PFS) significantly reduces exposure when keys are compromised. PFS generates a unique session key for every conversation, so a stolen key cannot decrypt past messages.
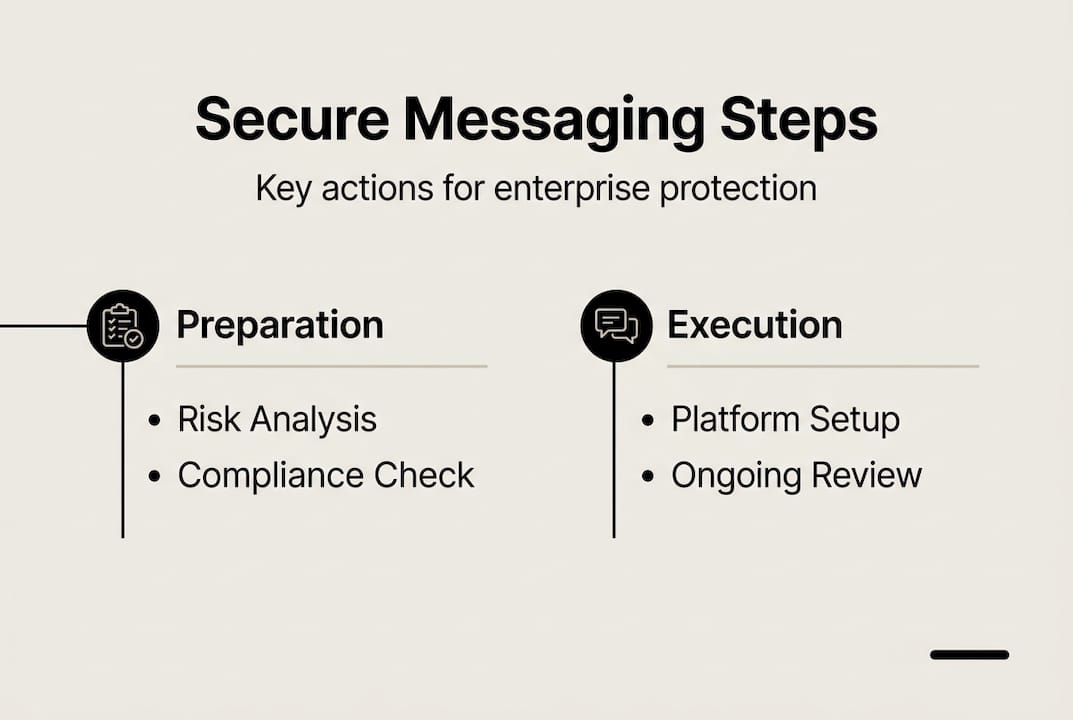
Follow these steps to select and pilot your messaging platform:
- Define your non-negotiables: List required certifications (SOC 2 Type II, ISO 27001), compliance features, and integration needs before evaluating any vendor.
- Request a security architecture review: Ask vendors for documentation on their encryption implementation, key management, and incident response procedures.
- Evaluate admin controls: Confirm the platform offers granular permissions, remote wipe, and centralized policy enforcement.
- Require penetration test results: Any credible enterprise vendor should provide recent third-party pen test reports.
- Run a controlled pilot: Deploy to a single department for 30 to 60 days. Monitor for usability issues, security gaps, and compliance gaps before full rollout.
"Enterprises should prioritize MLS for scalable group chats, with Signal Protocol for 1:1 communications. Key rotation and post-compromise security are not optional features. They are baseline requirements for any enterprise deployment." — RFC9750
For a full breakdown of what to look for, the must-have secure messaging features guide covers every critical capability. You can also explore secure business messaging solutions built specifically for enterprise environments, and review data security in messaging to understand how leading platforms handle data protection at scale.
Pro Tip: Never accept a vendor's self-reported security claims at face value. Require SOC 2 Type II and ISO 27001 certifications, and ask specifically whether penetration testing is conducted by an independent third party.
Integrate compliance, audit, and workflow controls
With platforms in place, layering compliance and audit mechanisms is essential for regulatory assurance and incident response. A secure platform without proper controls is like a vault with the door left open.
Start with your compliance framework. Work through these steps to deploy the right controls:
- Configure retention policies: Set automated message retention and deletion schedules aligned to your regulatory requirements (HIPAA, FINRA, GDPR, etc.).
- Enable eDiscovery integrations: Connect your messaging platform to your legal hold and eDiscovery tools so messages can be retrieved on demand.
- Enforce data residency: Use platform settings or regional data centers to ensure messages stay within required geographic boundaries.
- Activate audit logging: Enable comprehensive logs that capture who sent what, when, from which device, and whether it was read or forwarded.
- Deploy anomaly detection: Configure alerts for unusual access patterns, such as bulk message exports or logins from unrecognized locations.
The compliance landscape is shifting fast. By 2028, 80% of DCGA customers will require advanced archiving for chats and SMS, according to Gartner. If your current platform cannot support that, you are already behind.
"Advanced archiving is no longer a premium feature. It is becoming a baseline expectation for enterprise messaging compliance by 2028." — Gartner
Beyond compliance, your workflow needs operational safeguards. These policy frameworks protect collaboration without slowing teams down:
- Data Loss Prevention (DLP): Block or flag messages containing sensitive data patterns, such as credit card numbers, Social Security numbers, or proprietary code.
- Geo-fencing: Restrict message access based on user location, particularly useful for teams operating in high-risk regions.
- Multi-channel fallback: Define backup communication channels for when primary messaging systems experience outages.
- Role-based access controls: Limit who can create channels, add external users, or export message history.
- Incident response playbooks: Document exactly what happens when a messaging breach or policy violation is detected.
For a structured approach to policy enforcement, the enterprise messaging best practices guide provides a practical framework. You can also explore confidential messaging tips for handling sensitive internal communications, and see how messaging drives digital transformation when compliance is built into the workflow from the start. Authentication standards from NIST SP 800-63B provide a reliable benchmark for identity verification requirements.
Test, monitor, and continuously improve secure workflows
After integration, rigorous testing and ongoing improvement are where secure workflows become resilient and impactful for enterprise teams. Deployment is not the finish line. It is the starting point.
Begin with a structured verification process:
- Run penetration tests: Engage an independent security firm to attempt to breach your messaging environment. Test for man-in-the-middle attacks, session hijacking, and unauthorized data exports.
- Simulate post-compromise scenarios: Test what happens if a user account is compromised. Verify that key rotation limits the blast radius and that audit logs capture the incident accurately.
- Validate compliance controls: Confirm that retention policies, eDiscovery retrieval, and data residency enforcement all function as configured.
- Benchmark workflow impact: Measure hours saved, reduction in compliance incidents, and user adoption rates. DingTalk saved 5,000 hours per year through streamlined approvals, while Aapoon avoided $17.5M in HIPAA fines with compliant messaging.
- Review audit logs for anomalies: Establish a baseline for normal messaging behavior, then flag deviations for investigation.
Ongoing monitoring is what separates a secure workflow from a secure-at-launch workflow. Blockchain audit logs detect messaging breaches 38% faster than traditional logging methods, according to Gartner. If your platform supports immutable audit trails, enable them.
Strong encryption alone can reduce messaging exposure by up to 60%, but only when paired with consistent monitoring and policy enforcement. Encryption without visibility is incomplete protection.
For real-world examples of how enterprises have built and scaled secure workflows, secure messaging solution examples provides case studies worth reviewing.
Pro Tip: Schedule quarterly workflow reviews and include cross-team feedback from legal, HR, and operations, not just IT. The people using the system daily often spot friction points and security gaps that technical audits miss.
Advanced secure messaging solutions for enterprise teams
Building a secure messaging workflow is a significant undertaking, and the right platform makes every step more manageable. Luxenger is built specifically for enterprises that need bank-grade security, full compliance support, and AI-powered features that actually improve how teams work.
Luxenger combines enterprise messaging features like end-to-end encryption, AI-powered conversation summaries, real-time translation, and voice huddles with the compliance controls your organization requires. Whether you are managing a multilingual global team or enforcing strict data residency policies, the platform is designed to handle it. Explore the enterprise messaging platform to see how Luxenger maps to the workflow steps covered in this guide, or visit Luxenger to start a conversation with the team.
Frequently asked questions
What is the most critical security feature for enterprise messaging workflows?
E2EE secures message content at every stage of transmission, making it the foundational requirement for protecting enterprise communications from unauthorized access. Without it, even strong authentication controls leave message content exposed.
How can enterprises ensure compliance with retention and data residency rules?
Use platforms with automated retention policies, native eDiscovery integrations, and regional data center options. 80% of DCGA customers will require advanced archiving by 2028, so your platform needs to support that capability now.
What authentication measures prevent unauthorized internal message access?
Multi-factor authentication, FIDO2 hardware keys, and device attestation are the current best practices. MFA and device attestation together significantly reduce the risk of unauthorized access even when credentials are stolen.
Are consumer messaging apps safe for enterprise use?
Consumer apps lack enterprise controls such as audit logging, eDiscovery support, and centralized policy enforcement, making them a serious liability for sensitive internal communications.
How often should secure messaging workflows be tested and reviewed?
Review workflows quarterly and immediately after any major platform update or security incident. Regular reviews catch configuration drift and ensure your controls keep pace with evolving threats and compliance requirements.
