Many IT managers believe confidential messaging simply means using any encrypted chat app. The reality is far more complex. True confidential messaging for enterprises requires end-to-end encryption combined with compliance controls, metadata protection, and administrative oversight. Without understanding these layers, organizations risk exposing sensitive communications despite using supposedly secure tools. This guide explains how confidential messaging works technically, addresses compliance challenges, and helps you select platforms that balance security with operational needs.
Table of Contents
- Key takeaways
- What is confidential messaging and how does it work?
- Balancing confidentiality with enterprise compliance and operational needs
- Performance and future-proofing confidential messaging
- Choosing the right confidential messaging platform for your enterprise
- Discover secure confidential messaging solutions for enterprises
- Frequently asked questions about confidential messaging
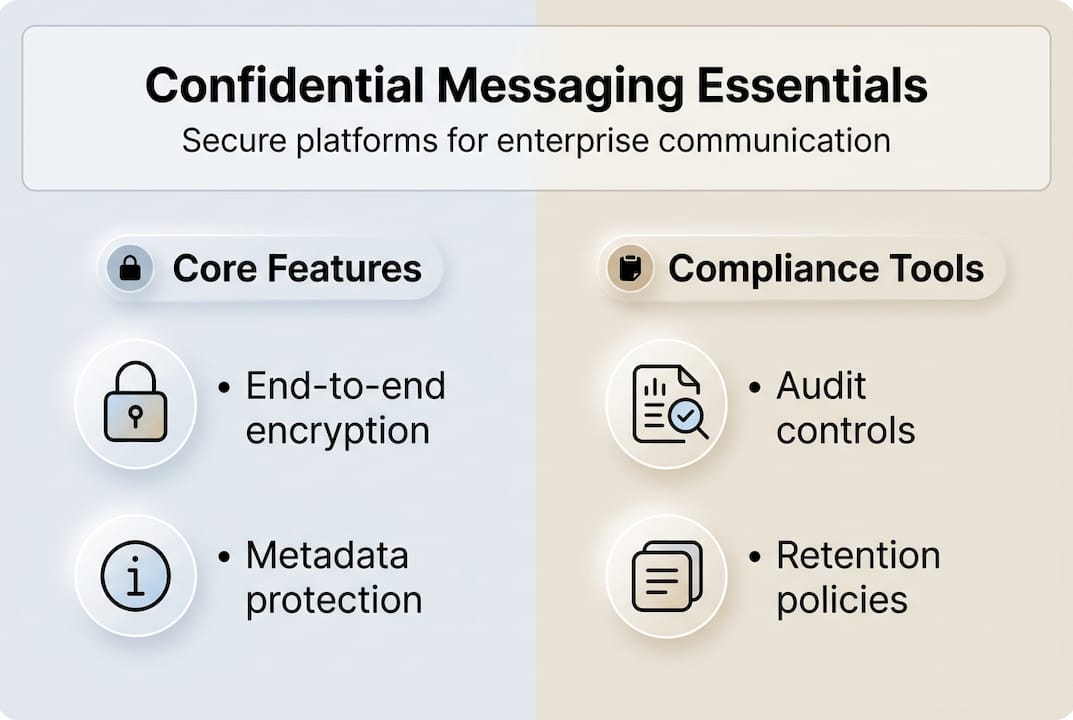
Key Takeaways
| Point | Details |
|---|---|
| End to end encryption | True confidential messaging ensures only sender and recipient can read content and blocks the service provider from accessing messages. |
| Compliance and oversight | Enterprise tools must pair end to end encryption with audit trails data retention policies and administrative controls. |
| Hybrid encryption models | Organizations can encrypt message content while enabling encrypted audit logs to satisfy security and compliance needs. |
| Metadata protection | Metadata remains a key vulnerability even with strong encryption and requires reduced data collection and features like sealed sender. |
| Established protocols | Verify platforms implement established cryptographic protocols such as the Signal Protocol rather than proprietary schemes. |
What is confidential messaging and how does it work?
Confidential messaging refers to secure internal communication tools using end-to-end encryption that ensure only sender and recipient can access message content. Unlike standard encrypted connections that protect data in transit, confidential messaging prevents even the service provider from reading messages. This distinction matters critically for enterprises handling sensitive intellectual property, financial data, or regulated information.
The technical foundation relies on sophisticated cryptographic protocols. Mechanics involve asymmetric key exchange, symmetric encryption per message, forward secrecy, and session key rotation. When you send a confidential message, your device generates a unique session key using protocols like X3DH (Extended Triple Diffie-Hellman). This key exchange happens automatically without user intervention.
Once keys are established, each message gets encrypted using AES-256 symmetric encryption. The Double Ratchet algorithm continuously generates new encryption keys for every message, providing forward secrecy. If an attacker compromises one key, they cannot decrypt past or future messages. This post-compromise security proves essential for long-term confidentiality.
Session key rotation happens frequently, sometimes with every message exchange. Modern enterprise platforms implement these protocols seamlessly:
- Asymmetric encryption for initial key exchange between devices
- Symmetric encryption (typically AES-256) for actual message content
- Continuous key rotation to maintain forward and backward secrecy
- Device-level key storage preventing server access to decryption keys
For enterprises, understanding these mechanisms helps evaluate vendor claims. A platform offering secure messaging must implement all these layers, not just transport layer security. The encryption should happen on sender devices before transmission and decryption only on recipient devices after delivery.
Pro Tip: Verify that your messaging platform uses established protocols like Signal Protocol or equivalent. Proprietary encryption schemes often contain undiscovered vulnerabilities that compromise confidentiality.
Balancing confidentiality with enterprise compliance and operational needs
End-to-end encryption protects message content brilliantly, but enterprises face additional requirements that pure encryption cannot address alone. Regulatory frameworks like HIPAA, GDPR, and FedRAMP demand audit trails, data retention policies, and administrative oversight. These compliance needs create tension with absolute confidentiality.

Enterprise tools use E2EE with compliance features and admin controls while maintaining confidentiality. The solution involves hybrid cryptographic models. Organizations can implement encryption for message content while maintaining encrypted audit logs that administrators can access under specific conditions. This approach satisfies both security teams demanding confidentiality and compliance officers requiring oversight.
Metadata presents another critical vulnerability. Metadata remains a key vulnerability despite E2EE; minimal collection and sealed sender features help mitigate risks. Even with perfectly encrypted content, metadata reveals who communicates with whom, when, how frequently, and from which locations. This information can expose organizational structures, project teams, and sensitive relationships.
Consider these enterprise-specific challenges:
- Legal hold requirements for litigation may conflict with message deletion features
- Data residency regulations require knowing where encrypted messages are stored
- Administrative password resets must not compromise message confidentiality
- Integration with existing identity management systems while maintaining encryption
Advanced platforms address metadata exposure through sealed sender technology, which anonymizes sender information during transmission. The recipient's device only learns the sender identity after decrypting the message. This prevents the service provider from building social graphs of organizational communications.
Hybrid models allow organizations to maintain encrypted backups with escrow keys held by designated security officers. These keys remain separate from operational systems and require multi-party authorization to access. This satisfies regulatory requirements for data preservation without giving the platform provider access to messages.
Pro Tip: Evaluate platforms offering configurable retention policies that maintain encryption throughout the data lifecycle. The ability to set different retention rules for different teams or message types provides flexibility while meeting secure messaging features requirements.
Choosing enterprise messaging solutions requires understanding these tradeoffs. Pure consumer-focused encrypted messengers often lack the administrative controls enterprises need. Conversely, traditional enterprise communication tools may sacrifice confidentiality for management visibility.
Performance and future-proofing confidential messaging
IT managers often worry that strong encryption will degrade messaging performance or create user friction. Testing reveals these concerns are largely unfounded with modern implementations. Performance overhead of encryption is minimal on modern hardware, with real-world latency acceptable even on constrained networks.
Benchmark data shows encryption operations complete in milliseconds. Signal Protocol implementations typically add less than 50ms latency per message on standard mobile devices. For enterprises with high-speed networks and recent hardware, this overhead becomes imperceptible. Even organizations with remote workers on slower connections report no noticeable performance impact.
Real-world performance depends on several factors beyond pure cryptographic speed:
| Performance Factor | Impact Level | Mitigation Strategy |
|---|---|---|
| Network Bandwidth | Medium | Compress messages before encryption |
| Device CPU Power | Low | Use hardware-accelerated encryption |
| Key Exchange Overhead | Low | Cache session keys appropriately |
| Attachment Encryption | Medium | Implement chunked encryption for large files |
The future presents new challenges requiring proactive planning. Quantum computers threaten current public key cryptography systems. While practical quantum attacks remain years away, hybrid models and post-quantum cryptography offer better future-proofing without sacrificing confidentiality. Forward-thinking enterprises should prioritize platforms with quantum-resistant encryption roadmaps.
Implementing future-proof confidential messaging involves these steps:
- Assess current cryptographic algorithms used by your messaging platform
- Verify the vendor has published plans for post-quantum cryptography migration
- Ensure the platform supports hybrid encryption combining classical and quantum-resistant algorithms
- Test performance impact of quantum-resistant algorithms in your environment
- Establish policies for cryptographic agility allowing algorithm updates without service disruption
NIST has standardized post-quantum cryptographic algorithms, and leading platforms are beginning implementation. The transition will happen gradually through hybrid approaches that use both traditional and quantum-resistant algorithms simultaneously. This ensures security against both current and future threats.
Pro Tip: Request your messaging vendor's cryptographic roadmap during evaluation. Platforms without clear plans for post-quantum migration may require costly replacements within five years. Following messaging security best practices includes planning for cryptographic evolution.
Performance monitoring should track encryption overhead as part of regular platform health checks. Sudden increases in latency may indicate cryptographic implementation issues or attacks. Establish baseline metrics and alert thresholds to catch problems early.
Choosing the right confidential messaging platform for your enterprise
Selecting a confidential messaging platform requires evaluating multiple dimensions beyond just encryption strength. IT managers should prioritize E2EE with admin controls, data sovereignty, and compliance features over consumer apps. The right platform balances security, usability, compliance, and operational requirements specific to your organization.
Start with these critical evaluation criteria:
- Verified end-to-end encryption using established protocols
- Compliance certifications matching your regulatory requirements (HIPAA, GDPR, FedRAMP, SOC 2)
- Administrative controls for user management without compromising message confidentiality
- Metadata minimization features like sealed sender and minimal logging
- Data sovereignty options including on-premises or private cloud deployment
- Audit capabilities providing visibility without breaking encryption
Comparing leading platforms reveals significant differences in how they balance these requirements:
| Platform Type | Encryption Strength | Compliance Features | Metadata Protection | Enterprise Controls |
|---|---|---|---|---|
| Consumer Messengers | Excellent | Minimal | Limited | None |
| Traditional Enterprise Tools | Variable | Excellent | Poor | Extensive |
| Modern Enterprise Secure Platforms | Excellent | Strong | Good | Comprehensive |
Data sovereignty concerns drive many enterprises toward platforms offering on-premises deployment or private cloud options. Hosting messaging infrastructure within your own data centers provides maximum control over data location and access. This matters particularly for organizations in regulated industries or operating across multiple jurisdictions with conflicting data laws.
Integration capabilities determine whether confidential messaging becomes isolated or enhances existing workflows. The platform should connect with your identity provider, support single sign-on, and integrate with productivity tools your teams already use. Poor integration creates friction that drives users toward unsanctioned communication channels.
Vendor transparency separates genuine security from marketing claims. Request detailed documentation of cryptographic implementations, independent security audits, and vulnerability disclosure policies. Reputable vendors publish security whitepapers and submit to third-party penetration testing.
Pro Tip: Conduct a proof of concept with your security team before organization-wide deployment. Test administrative controls, audit capabilities, and encryption verification in your actual environment. Many platforms that look strong on paper reveal limitations during hands-on evaluation.
Consider total cost of ownership beyond licensing fees. Factor in deployment costs, training requirements, integration development, and ongoing administration. A platform requiring extensive customization or generating high support tickets may cost more than alternatives with higher license fees but lower operational overhead.
Explore enterprise messaging solutions designed specifically for organizations balancing security and collaboration. Evaluate how different workplace messaging apps address your particular industry requirements and threat models.
Discover secure confidential messaging solutions for enterprises
Luxenger provides enterprise messaging built specifically for organizations requiring both confidentiality and collaboration. The platform combines bank-grade end-to-end encryption with AI-powered features that enhance productivity without compromising security. IT managers and security officers gain comprehensive administrative controls while employees enjoy seamless communication.
Unlike consumer messaging apps retrofitted for business use, Luxenger was designed from the ground up for enterprise requirements. The platform meets compliance standards including HIPAA and GDPR while offering features like AI-powered conversation summaries, voice huddles, and real-time translation. These capabilities help global teams collaborate effectively while maintaining strict confidentiality.
Explore Luxenger for enterprise operations to see how the platform addresses your specific security and collaboration needs. Review detailed Luxenger features including encryption protocols, administrative controls, and integration capabilities. Visit the security dashboard for comprehensive information about cryptographic implementations and compliance certifications.
Frequently asked questions about confidential messaging
What is the difference between secure messaging and confidential messaging?
Secure messaging refers broadly to any communication platform with security features like encrypted connections or access controls. Confidential messaging specifically means end-to-end encryption where only communicating parties can read messages, excluding even the service provider. All confidential messaging is secure, but not all secure messaging provides confidentiality.
How do enterprises mitigate metadata risks in confidential messaging?
Enterprises reduce metadata exposure by selecting platforms with minimal logging policies, sealed sender features that anonymize message routing, and data retention controls. Some organizations deploy on-premises messaging infrastructure to prevent any external metadata collection. Regular audits of metadata collection practices ensure platforms maintain privacy commitments over time. Following security best practices includes evaluating metadata protection as rigorously as content encryption.
Can encryption coexist with compliance auditing requirements?
Yes, through hybrid cryptographic models that maintain separate encryption for message content and audit logs. Enterprises can implement administrative access to encrypted metadata and audit trails without compromising message confidentiality. Escrow key systems allow authorized security officers to access archived messages under specific legal or compliance scenarios while preventing routine access by platform providers or administrators.
How do AI features integrate with confidential messaging?
AI-powered features like conversation summaries and translation can work with confidential messaging when processing happens on-device or within the encrypted environment. The AI never accesses plaintext messages on external servers. Modern platforms implement AI models that operate on encrypted data or run locally on user devices. This enables productivity enhancements while preserving confidentiality. Learn more about secure collaboration messaging that combines AI and encryption effectively.