Enterprises faced more than 5000 cyberattacks per day in 2025, yet many IT managers still believe all messaging apps offer equal security. This misconception puts sensitive enterprise data at serious risk. Secure messaging is not just another buzzword; it's a critical defense layer for protecting confidential communications in 2026. This guide clarifies what secure messaging truly means, why it matters for your organization, and how to implement it effectively without driving your team toward unauthorized Shadow IT solutions.
Table of Contents
- Understanding Secure Messaging And Its Role In Enterprises
- Challenges Enterprises Face With Messaging Security And Shadow IT
- Advanced Secure Messaging Protocols And Future-Proofing Security
- Implementing Secure Messaging Solutions Effectively In Your Organization
- Secure Your Enterprise Messaging With Luxenger
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Secure messaging protects enterprise communications | It combines encryption, authentication, and integrity controls to safeguard sensitive conversations from unauthorized access and tampering. |
| Human error causes most data breaches | 95% of breaches stem from mistakes, making secure messaging essential to reduce risks from unauthorized app usage and poor security practices. |
| Balancing security with usability prevents Shadow IT | High-friction security tools drive 67% more Shadow IT adoption, requiring platforms that combine strong protection with seamless user experience. |
| Advanced protocols like forward secrecy enhance protection | Modern secure messaging uses Continuous Key Agreement and post-quantum considerations to future-proof enterprise communications. |
| Implementation requires cross-functional teams | Successful deployment needs diverse perspectives from IT, executives, and end users, plus clear success metrics and robust infrastructure support. |
Understanding secure messaging and its role in enterprises
Secure messaging protects the confidentiality and integrity of your enterprise communications through multiple security layers. At its core, it ensures that only intended recipients can read messages and that no one can alter content without detection. This goes far beyond password protection or basic SSL connections used by consumer apps.
Encryption forms the foundation of secure messaging, but not all encryption is equal. End-to-end encryption means messages are encrypted on the sender's device and only decrypted on the recipient's device, with no intermediary including the service provider able to access plaintext content. Transport encryption only protects messages in transit, leaving them vulnerable at rest on servers.
Authentication prevents unauthorized access by verifying user identities before granting message access. This typically combines password credentials with two-factor authentication, biometric verification, or hardware security keys. Without proper authentication, encryption becomes meaningless because attackers can simply impersonate legitimate users.
The stakes are enormous for enterprises. 95% of all data breaches are caused by human error, and unsecured messaging creates countless opportunities for mistakes. An employee sharing confidential product plans through an unencrypted consumer app, a contractor forwarding sensitive client data to personal email, or a manager discussing merger details on an insecure platform can each trigger catastrophic breaches.
Key security elements in enterprise messaging include:
- End-to-end encryption ensuring only intended recipients access message content
- Forward secrecy protecting past messages even if current encryption keys are compromised
- Message integrity verification detecting any unauthorized alterations
- Access controls limiting who can join conversations or channels
- Audit trails tracking message history for compliance and security reviews
Secure messaging mitigates risks by creating a controlled environment where IT teams can enforce security policies, monitor for suspicious activity, and ensure compliance with industry regulations. It transforms messaging from a vulnerability into a defendable asset.
Challenges enterprises face with messaging security and Shadow IT
Even with approved secure messaging platforms, 43% of UK businesses experience unauthorized messaging app usage by staff. This creates fragmented communication channels where sensitive information flows through unmonitored, insecure consumer apps like WhatsApp, Telegram, or personal email accounts. Each unauthorized channel represents a potential breach point outside IT visibility and control.

The primary driver of this Shadow IT behavior is security friction. When approved platforms require multiple authentication steps, impose strict file-sharing limits, or deliver poor user experiences, employees naturally seek easier alternatives. Organizations with high-friction security tools experience 67% higher rates of Shadow IT adoption, creating a dangerous paradox where excessive security measures actually reduce overall security posture.
Common friction points that push users toward Shadow IT include:
- Cumbersome login processes requiring frequent re-authentication
- Slow message delivery or unreliable notifications
- Confusing user interfaces that require extensive training
- Limited integration with existing workflow tools
- Restrictive file-sharing capabilities that hinder collaboration
Pro Tip: Shadow IT is a symptom, not a disease. If employees bypass your secure messaging platform, the platform likely fails to meet their real collaboration needs. Survey your team to identify specific pain points before blaming users for security violations.
Security experts emphasize that usability and security must coexist. As one cybersecurity analyst noted: "The most secure system in the world is worthless if nobody uses it. Enterprises must prioritize platforms that deliver bank-grade security through intuitive interfaces that feel invisible to end users."
The consequence of poor messaging security adoption extends beyond data breaches. It fragments institutional knowledge across disconnected platforms, creates compliance gaps when auditors cannot access complete communication records, and wastes IT resources managing multiple unauthorized tools. Solving this requires security best practices for IT admins that balance protection with genuine usability.
Advanced secure messaging protocols and future-proofing security
Modern secure messaging protocols implement Continuous Key Agreement as a core component providing Forward Secrecy and Post-Compromise Security. These advanced features distinguish enterprise-grade platforms from basic encrypted messaging apps.
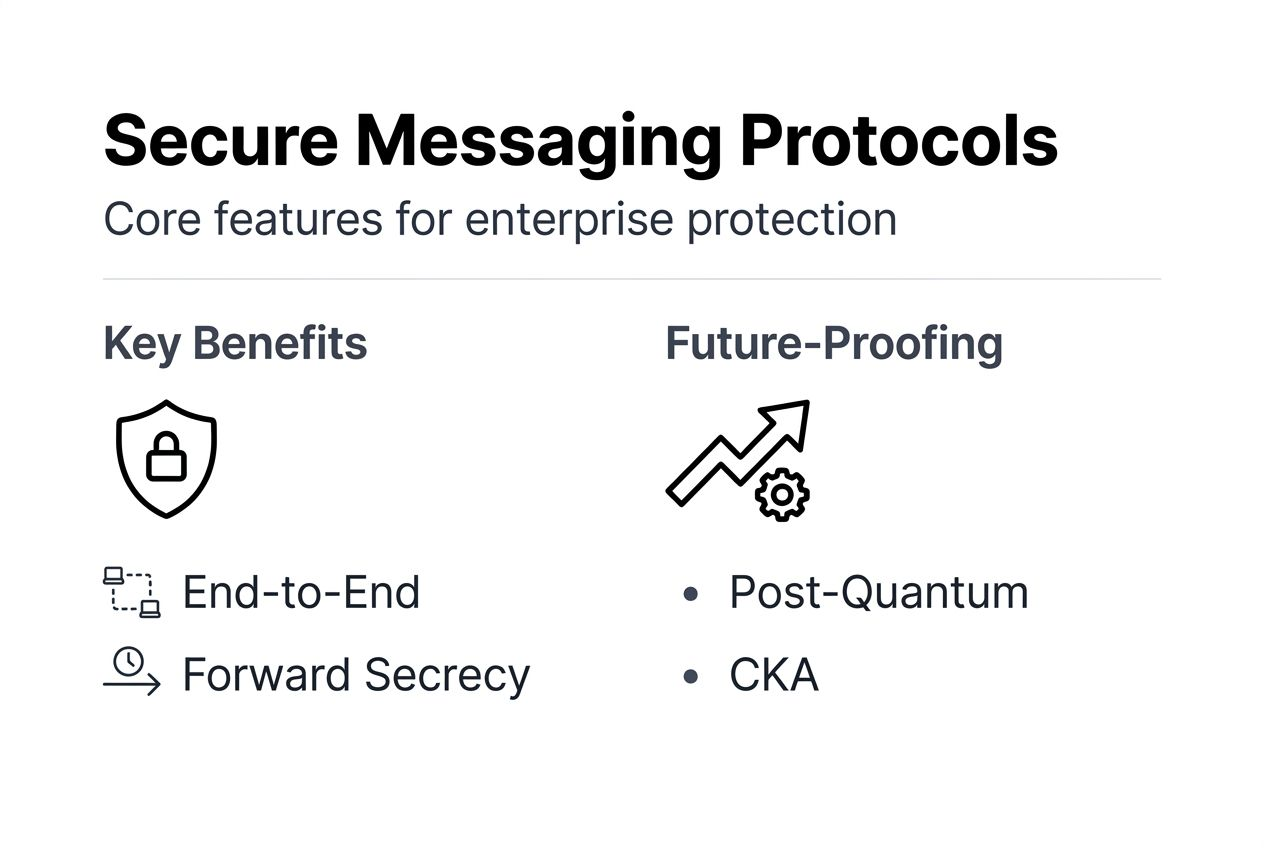
Continuous Key Agreement (CKA) means encryption keys constantly update throughout a conversation rather than remaining static. Each message uses a unique key derived from the previous exchange, creating an evolving encryption chain. This approach delivers two critical security properties that protect enterprises from sophisticated attacks.
Forward Secrecy ensures that compromising current encryption keys cannot decrypt past messages. If an attacker steals today's keys, they cannot retroactively access yesterday's communications because those used completely different keys that no longer exist. This protects historical conversations even after security breaches.
Post-Compromise Security means the system automatically recovers from key compromises without manual intervention. After an attacker obtains current keys, the CKA protocol generates new keys through subsequent legitimate messages, eventually locking out the attacker. This self-healing property limits breach windows and reduces incident response costs.
The quantum computing threat adds urgency to protocol selection. Classical secure messaging protocols face potential vulnerabilities as quantum computers mature, though practical attacks remain years away. Post-quantum protocols offer stronger mathematical foundations resistant to quantum decryption, but they come with significant tradeoffs.
| Protocol Type | Communication Overhead | Current Security Level | Quantum Resistance |
|---|---|---|---|
| Classical (e.g., Signal Protocol) | Low (< 5 KB per exchange) | Very High | Vulnerable to future quantum attacks |
| Post-Quantum | High (> 50 KB per exchange) | Very High | Resistant to quantum computing threats |
The 10x communication overhead in post-quantum protocols creates practical deployment challenges for enterprises. Larger key exchanges consume more bandwidth, increase latency, and strain network infrastructure, especially for organizations with remote workers on limited connections or global teams across constrained networks.
Pro Tip: Most enterprises should prioritize classical protocols with strong CKA implementations in 2026 rather than rushing to post-quantum solutions. The quantum threat remains theoretical while network performance impacts are immediate. Monitor quantum computing developments and plan migration timelines, but don't sacrifice user experience for premature protection.
As protocols evolve, focus on platforms that demonstrate commitment to security research, publish transparent cryptographic specifications, and maintain clear upgrade paths. The right provider will balance cutting-edge protection with practical deployment realities.
Implementing secure messaging solutions effectively in your organization
Successful implementation requires assembling a diverse project team including end users, IT personnel, security specialists, and executives. Each perspective contributes essential insights. End users identify workflow friction points, IT staff assess infrastructure requirements, security teams evaluate threat models, and executives ensure alignment with business objectives.
Follow these evaluation and selection steps:
- Define specific security requirements based on industry regulations and threat landscape
- Identify essential collaboration features your teams actually use daily
- Test candidate platforms with diverse user groups across departments
- Evaluate vendor security certifications, audit reports, and incident response history
- Assess total cost of ownership including licenses, infrastructure, training, and ongoing support
- Verify integration capabilities with existing tools like email, calendars, and project management systems
Network infrastructure often determines success or failure. Reliable wireless infrastructure is essential because poor networks cause message delays or delivery failures that drive users back to unreliable consumer apps. Conduct thorough network assessments before rollout, especially for organizations with remote workers, multiple office locations, or BYOD policies.
Establish clear success metrics before deployment. Vague goals like "improve security" or "enhance collaboration" provide no accountability. Instead, define measurable targets such as:
- Reduce unauthorized messaging app usage by 80% within six months
- Achieve 95% daily active user rate among target departments
- Decrease average message response time by 40%
- Maintain zero security incidents related to messaging within first year
- Complete compliance audits with full message trail visibility
Training and ongoing support determine long-term adoption. Schedule hands-on sessions where users practice real scenarios rather than watching passive demonstrations. Create role-specific training addressing how each department uses messaging differently. Establish accessible support channels where users can quickly get help without switching platforms.
Pro Tip: Launch with a pilot group of enthusiastic early adopters who can become internal champions. Their success stories and peer support prove far more persuasive than top-down mandates. Integrate continuous feedback loops to identify and fix friction points before they drive Shadow IT behavior.
For comprehensive implementation guidance, explore Luxenger for enterprise operations, remote team communication tips, and our detailed enterprise messaging security best practices guide.
Secure your enterprise messaging with Luxenger
Luxenger delivers bank-grade security without sacrificing the seamless collaboration your teams need. Our platform combines end-to-end encryption, Continuous Key Agreement protocols, and advanced access controls with AI-powered summaries, voice huddles, and real-time translation across 100+ languages. This unique combination eliminates the security-versus-usability tradeoff that drives Shadow IT adoption.
Designed specifically for medium to large enterprises, Luxenger provides the robust security features covered in this guide while maintaining the intuitive experience that ensures actual adoption. Our comprehensive admin dashboard gives IT teams full visibility and control without creating friction for end users.
Explore how Luxenger for enterprise operations addresses your specific security and collaboration needs. Review our complete enterprise messaging features and examine detailed security specifications through our security dashboard. See why leading organizations choose Luxenger as their secure messaging foundation.
Frequently asked questions
What differentiates secure messaging from regular messaging apps?
Secure messaging implements end-to-end encryption, forward secrecy, and authentication controls that prevent unauthorized access to message content. Regular messaging apps typically use only transport encryption, leaving messages vulnerable on servers and lacking advanced security protocols like Continuous Key Agreement. Enterprise secure messaging also provides admin controls, audit trails, and compliance features absent from consumer apps.
How does forward secrecy protect messages?
Forward secrecy generates unique encryption keys for each message or session that are discarded after use. If an attacker compromises current keys, they cannot decrypt past messages because those keys no longer exist anywhere in the system. This protects historical communications even after security breaches, limiting damage from key compromise incidents.
Why do employees use unauthorized apps despite secure options?
Excessive security friction in approved platforms drives employees toward easier alternatives. When legitimate tools require cumbersome authentication, deliver poor performance, or lack essential features, users naturally seek Shadow IT solutions that let them work efficiently. The root cause is usually poor platform usability rather than employee negligence.
What future trends impact secure messaging security?
Quantum computing poses long-term threats to classical encryption protocols, driving development of post-quantum secure messaging. AI-powered threat detection will identify suspicious messaging patterns in real time. Zero-trust architecture will expand from network security into messaging platforms. Regulatory compliance requirements will continue tightening, especially for industries handling sensitive personal data.
How to measure success after implementing secure messaging?
Track daily active user rates to ensure actual adoption rather than forced compliance. Monitor Shadow IT usage through network analysis to verify employees stopped using unauthorized apps. Measure average message response times and collaboration metrics to confirm productivity improvements. Review security incident reports to validate reduced breach risks. Conduct user satisfaction surveys to identify remaining friction points before they drive workarounds.
