Selecting the right workplace messaging app has become a critical decision for IT and communications managers. With 67% higher shadow IT adoption in organizations using high-friction security tools, the stakes are clear. Many platforms claim to offer secure, AI-powered collaboration, but they differ dramatically in architecture, privacy models, and metadata handling. Understanding these differences helps you make informed choices that balance security with usability, ensuring your team actually uses the tools you deploy instead of finding workarounds that compromise enterprise data.
Table of Contents
- Evaluating Workplace Messaging Apps: Key Criteria For 2026
- Centralized Messaging Apps: Slack, Microsoft Teams, And WhatsApp
- Federated And Decentralized Apps: Matrix Ecosystem, Signal, And Telegram
- Head-To-Head Comparison: Features, Privacy, And AI Capabilities
- Choosing The Right Workplace Messaging App For Your Enterprise Needs
- Discover Luxenger: Secure, AI-Powered Business Messaging For Enterprises
Key takeaways
| Point | Details |
|---|---|
| Architecture matters | Centralized, federated, and decentralized platforms offer distinct trade-offs in control, privacy, and resilience for enterprise deployments. |
| Metadata is critical | How platforms handle user metadata directly impacts compliance posture and privacy protections beyond message encryption alone. |
| Usability prevents shadow IT | Balancing robust security with intuitive interfaces reduces unauthorized app usage and improves organization-wide adoption rates. |
| AI enhances collaboration | Advanced AI features like conversation summaries and workflow automation boost productivity when integrated thoughtfully with existing tools. |
| Integration capabilities count | Seamless connections to enterprise systems determine whether messaging platforms support or disrupt established workflows and processes. |
Evaluating workplace messaging apps: key criteria for 2026
Before diving into specific platforms, establish clear evaluation criteria. Security remains paramount, but it must work alongside usability. Organizations with high-friction security tools experience 67% higher rates of shadow IT adoption, creating the exact vulnerabilities you're trying to prevent. Your evaluation framework should address multiple dimensions simultaneously.
Start with encryption standards and metadata handling. End-to-end encryption protects message content, but metadata like contact lists, usage patterns, and IP addresses can reveal sensitive organizational information. Understanding secure messaging platforms must-have features helps you assess what truly matters for enterprise deployments.
Architecture fundamentally shapes control and resilience. Centralized platforms offer simplicity but create single points of failure. Federated systems distribute control across multiple servers while maintaining interoperability. Decentralized architectures remove central authorities entirely, though implementation complexity increases. Each model affects data sovereignty, compliance requirements, and operational continuity differently.
AI-powered features now separate leading platforms from basic messaging tools. Conversation summaries, automated workflows, and intelligent search capabilities enhance productivity when implemented well. However, AI features that require cloud processing may conflict with strict data residency requirements. Evaluate how AI capabilities align with your security policies and enterprise messaging security best practices.
Integration capabilities determine whether a messaging platform becomes your collaboration hub or another isolated tool. Consider these evaluation points:
- API availability and rate limits for custom integrations
- Native connections to productivity suites, project management tools, and CRM systems
- Single sign-on support and directory synchronization
- Webhook capabilities for event-driven workflows
- Export and backup options for compliance and disaster recovery
Pro Tip: Create a weighted scorecard with your specific requirements before evaluating vendors. Assign higher weights to non-negotiable criteria like compliance certifications or specific encryption standards to make objective comparisons.
Centralized messaging apps: Slack, Microsoft Teams, and WhatsApp
Centralized platforms dominate enterprise messaging because they offer familiar interfaces and broad adoption. Slack, Microsoft Teams, and WhatsApp represent this category, but each carries distinct limitations that IT managers must understand.
Slack provides extensive integrations and user-friendly collaboration features, but its unstructured data model hinders effective incident management compared to dedicated platforms. When critical incidents occur, the lack of structured data attributes makes it difficult to track resolution workflows, assign responsibilities, or generate compliance reports. This architectural choice prioritizes flexibility over operational rigor.
WhatsApp uses the Signal Protocol for message encryption but collects extensive metadata retained by Facebook/Meta. For enterprises handling sensitive information, this metadata collection creates compliance risks. Contact lists, usage patterns, and device information flow to Meta's servers regardless of message encryption, potentially violating data protection regulations in certain jurisdictions.
Centralization creates operational risks that scale with organizational size. API rate limiting can disrupt critical integrations during peak usage. Data fragmentation occurs when different teams use different channels without governance. Vendor lock-in increases as workflows become deeply embedded in platform-specific features. When evaluating comparisons between Slack and alternatives, consider these long-term dependencies.
Key limitations of centralized platforms include:
- Single vendor controls all data, creating dependency and potential service disruptions
- Metadata collection often exceeds what's necessary for platform functionality
- Scaling costs increase predictably with user count and feature requirements
- Limited customization options constrain unique enterprise workflows
- Compliance complexity grows with international data residency requirements
Pro Tip: If you must use centralized platforms, implement data loss prevention tools and establish clear channel governance policies. Regular audits of shared content and access permissions help maintain security posture despite architectural limitations.
Federated and decentralized apps: Matrix ecosystem, Signal, and Telegram
Federated and decentralized platforms offer different privacy and control models compared to centralized alternatives. Understanding these architectural differences helps you evaluate whether enhanced privacy justifies potential trade-offs in speed and feature availability.

Matrix is designed for decentralized communication with open APIs supporting instant messaging, VoIP, and IoT applications. The federated architecture allows organizations to run their own homeservers while maintaining interoperability with the broader Matrix network. This gives you data sovereignty without sacrificing connectivity. However, federation still centralizes data at homeserver level, requiring careful governance of who controls these servers.
Signal represents the gold standard for metadata minimization. While Signal minimizes metadata collection by design, its mobile-first architecture and limited enterprise management features make large-scale deployment challenging. The sealed sender feature prevents even Signal's servers from knowing who messages whom, offering exceptional privacy. Yet this comes with trade-offs in message delivery guarantees and multi-device synchronization complexity.
Telegram occupies a middle ground that often confuses enterprise buyers. Default cloud chats use server-side encryption, not end-to-end encryption. Only Secret Chats provide true end-to-end protection, and these don't sync across devices. The centralized server architecture contradicts Telegram's decentralized marketing, creating compliance risks for organizations assuming stronger privacy protections than actually exist.
Comparing privacy models across platforms:
| Platform | Encryption Model | Metadata Collection | Server Architecture | Enterprise Controls |
|---|---|---|---|---|
| Matrix | E2E optional, federated | Minimal, homeserver dependent | Federated homeservers | High, self-hosted options |
| Signal | E2E default, sealed sender | Minimal by design | Centralized Signal servers | Limited, consumer focused |
| Telegram | Server-side default, E2E optional | Moderate | Centralized cloud | Moderate, admin tools |
Federated networks distribute control but don't eliminate centralization entirely. Each homeserver becomes a point of control and potential failure. True decentralization requires peer-to-peer architectures or distributed governance models, which introduce complexity in user experience and message reliability. When planning digital workplace transformation strategies, weigh these architectural trade-offs against your specific security and usability requirements.
Pro Tip: If you choose Matrix for its federation benefits, invest in dedicated homeserver administration resources. The operational overhead of maintaining federation, managing encryption keys, and troubleshooting cross-server issues requires specialized expertise that many IT teams underestimate.
Head-to-head comparison: features, privacy, and AI capabilities
Comparing messaging platforms across multiple dimensions reveals patterns that guide selection. Security, privacy, AI capabilities, and enterprise suitability vary significantly, even among platforms marketing similar features.
Decentralized chat solutions offer enhanced privacy compared to centralized platforms, but this advantage comes with implementation complexity. Centralized apps trade privacy for integration breadth and user familiarity. Your organization's risk tolerance and technical capabilities determine which trade-offs make sense.
AI-driven collaboration features now differentiate leading platforms. Conversation summaries distill lengthy threads into actionable points. Automated workflow triggers connect messaging to task management. Intelligent search surfaces relevant context across channels. However, AI processing often requires cloud infrastructure, creating tension with data residency requirements. Evaluate whether AI-powered collaboration in team messaging aligns with your security policies before committing.
Platform comparison across key enterprise criteria:
| Feature | Slack | Matrix | Signal | Telegram |
|---|---|---|---|---|
| Default Encryption | In transit only | E2E optional | E2E default | Server-side |
| Metadata Protection | Extensive collection | Homeserver dependent | Minimal collection | Moderate collection |
| AI Capabilities | Advanced, cloud-based | Limited, emerging | None | Basic, cloud-based |
| Enterprise Admin Tools | Comprehensive | Moderate, self-managed | Limited | Moderate |
| Integration Ecosystem | Extensive | Growing, open APIs | Minimal | Moderate |
| Self-Hosting Option | No | Yes | No | No |
Shadow IT risks correlate directly with friction in approved tools. When security measures create usability barriers, employees find workarounds. The challenge isn't choosing the most secure platform in isolation but selecting one your team will actually use consistently. Balance these factors:
- Security controls that protect without impeding daily workflows
- Intuitive interfaces that minimize training requirements
- Mobile and desktop experiences that match consumer app quality
- Integration depth that eliminates context switching between tools
- AI features that demonstrably save time on routine tasks
Centralized platforms excel at integrations and familiar user experiences but concentrate risk. Decentralized architectures distribute control and enhance privacy but increase operational complexity. Your decision should reflect your organization's specific threat model, compliance requirements, and technical capabilities rather than following industry trends.
Choosing the right workplace messaging app for your enterprise needs
Selecting a messaging platform requires aligning technical capabilities with organizational culture and workflows. The challenge is finding a secure messaging solution your team will actually use, not just the one with the longest feature list.
Start by mapping current communication patterns. Which teams collaborate most frequently? What information sensitivity levels exist across departments? Where do current tools create friction or gaps? This assessment reveals whether you need a single enterprise-wide platform or can support multiple specialized tools for different use cases.
Follow this decision framework:
- Define non-negotiable security and compliance requirements based on your industry regulations and data classification policies.
- Identify must-have integrations with existing enterprise systems like CRM, project management, and productivity suites.
- Evaluate AI capabilities that align with your collaboration challenges, such as conversation summarization for distributed teams or automated workflow triggers.
- Test user experience through vendor demos and pilot programs with representative teams before committing to enterprise-wide deployment.
- Assess total cost of ownership including licensing, integration development, training, and ongoing administration over a three-year period.
- Plan change management and training programs to maximize adoption and minimize shadow IT emergence during transition.
Education plays a critical role in successful deployment. Teams resist new tools when they don't understand the value proposition. Communicate clearly why you selected a specific platform, how it protects organizational data, and what productivity benefits it delivers. Provide role-specific training that demonstrates relevant features rather than generic overviews.
Monitor usage patterns after deployment to identify adoption barriers early. Low engagement in specific departments may indicate usability issues, missing integrations, or inadequate training. Address these gaps quickly before shadow IT takes root. Regular feedback loops help you adjust policies and features to balance security with productivity.
Pro Tip: Establish clear governance policies before deployment. Define who can create channels, how long messages are retained, what data can be shared, and how external collaboration works. These policies prevent security incidents and compliance violations while giving teams clarity on appropriate usage.
Explore secure business messaging solutions for enterprises that combine robust security with practical usability. The right platform grows with your organization, adapting to evolving collaboration needs without compromising data protection.
Discover Luxenger: secure, AI-powered business messaging for enterprises
After evaluating messaging platform types and selection criteria, consider how Luxenger addresses the challenges discussed throughout this article. We built an enterprise-grade platform that combines bank-level security with AI-powered collaboration features your teams will actually use.
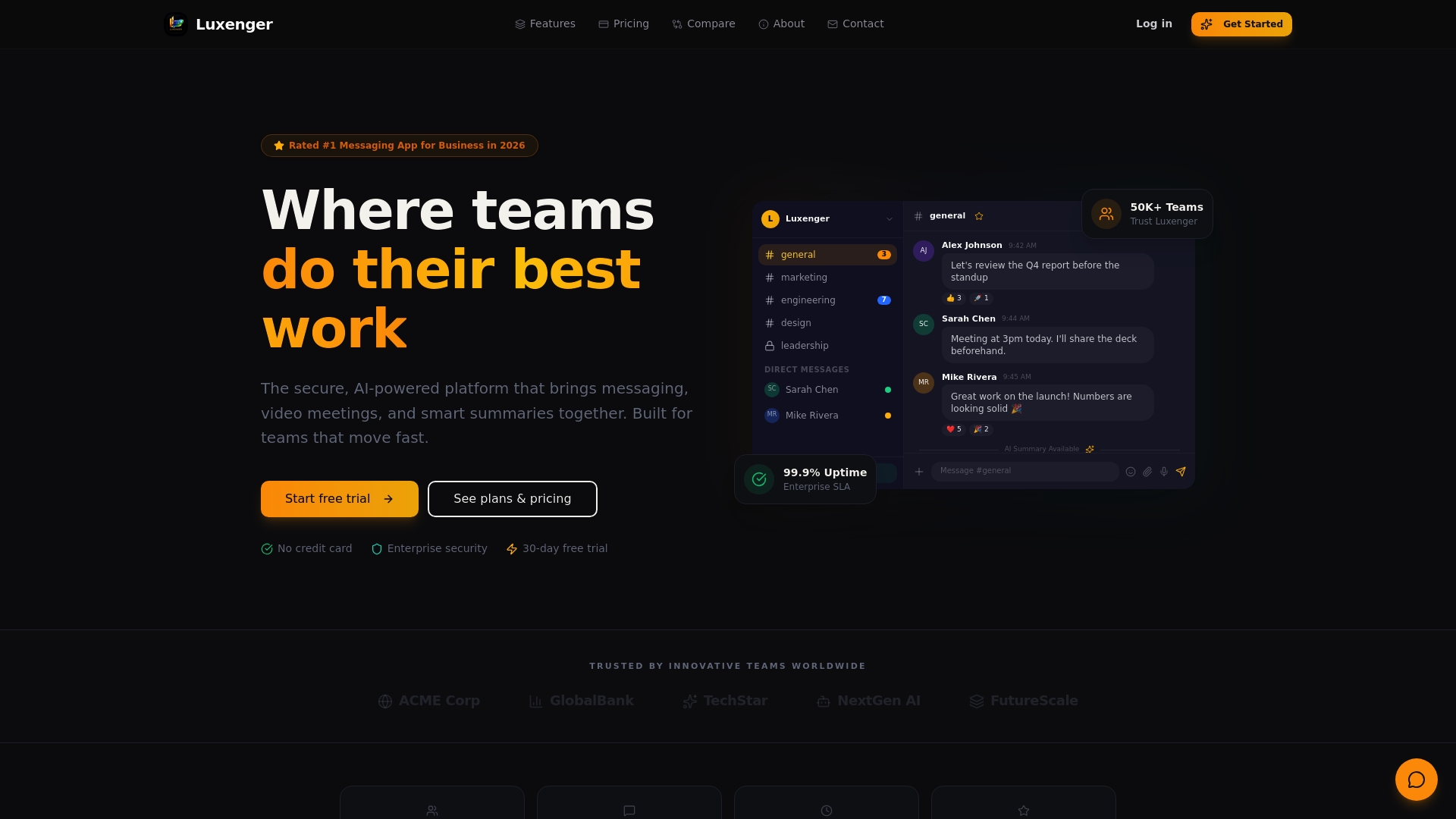
Luxenger delivers end-to-end encryption with minimal metadata collection, addressing privacy concerns without sacrificing functionality. Our AI capabilities include conversation summaries, real-time translation for global teams, and voice huddles for quick collaboration. These features integrate seamlessly with your existing enterprise workflows, reducing the friction that drives shadow IT adoption.
Our platform provides comprehensive admin dashboards for security monitoring and operational insights. You maintain control over data residency, user permissions, and compliance reporting while your teams enjoy intuitive interfaces that rival consumer messaging apps. Explore Luxenger enterprise messaging solutions to see how we balance security and usability. Review our platform features and security management tools to understand how Luxenger fits your specific requirements.
Frequently asked questions
What is the difference between federated and decentralized messaging?
Federated systems distribute control across multiple servers operated by different entities while maintaining interoperability through common protocols. Decentralized systems eliminate central controlling authorities entirely, often using peer-to-peer technology or distributed governance models. True decentralization requires no single point of control or failure, while federation still centralizes data at individual server levels.
How do metadata practices affect workplace messaging security?
Metadata includes information like contact lists, message timestamps, IP addresses, device identifiers, and usage patterns that platforms collect beyond message content. Even with strong encryption, extensive metadata collection creates privacy risks and potential compliance violations. Platforms with minimal metadata collection enhance security posture but may limit certain convenience features like cloud message synchronization across unlimited devices.
Why is shadow IT a concern with messaging apps in enterprises?
Shadow IT emerges when approved tools create too much friction through complex security controls or poor usability, prompting employees to adopt unauthorized alternatives. This increases security risks because IT teams can't monitor, protect, or control data flowing through unapproved channels. Organizations experience higher shadow IT rates when security measures significantly impede productivity, leading to data leakage and compliance violations.
Can AI features improve team collaboration in messaging apps?
AI capabilities like conversation summarization, automated workflow triggers, intelligent search, and real-time translation demonstrably enhance productivity when implemented thoughtfully. These features reduce time spent on routine tasks, help distributed teams overcome language barriers, and surface relevant context quickly. However, effectiveness depends on how well AI integrations align with existing workflows and whether they require cloud processing that conflicts with data residency requirements.