Selecting secure messaging for AI agents is no longer just about encryption. IT managers face complex privacy challenges as one-third of large enterprises now deploy AI agents, requiring solutions that protect data during computation, prevent post-access leaks, and ensure accountability across multi-agent interactions. Traditional access controls fall short when agents process sensitive information or collaborate autonomously. This guide examines evaluation criteria for secure agent messaging, explores leading frameworks like AgentCrypt and BlockA2A, and compares their features to help you choose solutions aligned with your enterprise's confidentiality requirements and compliance mandates in 2026.
Table of Contents
- How To Evaluate Secure Messaging For Agents: Essential Criteria
- Agentcrypt: A Multi-Tiered Framework For Encrypted Agent Communication
- Blocka2a: Decentralized Trust And Integrity For Multi-Agent Communication
- Comparing Secure Messaging Solutions For Agents: Features And Use Cases
- Explore Luxenger's Secure Messaging Solutions For Enterprises
Key takeaways
| Point | Details |
|---|---|
| Layered privacy controls | Secure messaging requires nuanced, role-based access beyond traditional binary permissions to address post-access risks. |
| Advanced frameworks available | AgentCrypt and BlockA2A offer encryption layers and decentralized trust models specifically designed for agent communication. |
| Enterprise adoption accelerating | One-third of large organizations already use AI agents, making secure messaging infrastructure a critical priority. |
| Evolving threat models | Perfect safety is challenging; solutions must adapt to emerging attack vectors and compliance requirements. |
| Feature comparison essential | Evaluating encryption levels, trust architecture, and auditability helps align solutions with enterprise needs. |
How to evaluate secure messaging for agents: essential criteria
When assessing secure messaging solutions for AI agents, look beyond basic encryption. Traditional access controls are insufficient for AI agents because privacy risks often emerge after data access occurs. Agents might inadvertently expose sensitive information during computation, store data insecurely, or share it with unauthorized parties. Your evaluation framework must address these post-access vulnerabilities.
Start by examining privacy granularity. Does the solution support role-based and context-aware controls that limit data exposure based on agent function and task requirements? Evaluate whether the platform protects data during computation itself, not just in transit or at rest. Homomorphic encryption, for instance, allows agents to process encrypted data without decryption, maintaining confidentiality throughout operations.
Message integrity and authenticity matter equally. Verify that solutions provide cryptographic guarantees ensuring messages remain unaltered and originate from verified sources. Accountability mechanisms like audit trails and immutable logs support compliance requirements and forensic investigations when incidents occur. Check whether the platform addresses agent-specific threats such as prompt injection attacks or behavioral manipulation.
Scalability and integration capabilities determine practical deployment success. Assess how easily the solution integrates with your existing enterprise messaging security best practices and infrastructure. Consider whether the architecture supports growing agent populations and increasing message volumes without performance degradation.
Pro Tip: Create a weighted scoring matrix for your evaluation criteria. Assign higher weights to factors most critical for your industry's compliance requirements, then score each solution objectively against these benchmarks.
Key evaluation dimensions include:
- Privacy preservation during computation and agent errors
- Encryption strength and flexibility across communication contexts
- Decentralization level and trust model architecture
- Attack resilience against agent-specific threat vectors
- Compliance alignment with industry standards and regulations
- Interoperability with existing enterprise systems and workflows
AgentCrypt: a multi-tiered framework for encrypted agent communication
AgentCrypt represents a sophisticated approach to agent messaging security through its layered privacy architecture. The framework offers four distinct privacy tiers ranging from unrestricted data exchange to fully encrypted computation using homomorphic encryption. This flexibility lets you match security controls precisely to each communication context and data sensitivity level.

The framework's most powerful feature is its ability to enable computation on encrypted data. Agents can process sensitive information, perform calculations, and generate insights without ever decrypting the underlying data. This capability addresses a fundamental weakness in traditional secure messaging where data becomes vulnerable during processing. Even when AI models make errors or behave unexpectedly, privacy of tagged data is preserved, ensuring compliance robustness across scenarios.
AgentCrypt implements fine-grained encryption policies that adapt to agent roles, task requirements, and data classification levels. You can configure different privacy tiers for various agent types within your organization. Customer service agents might operate at a lower encryption tier for routine queries, while financial analysis agents handling sensitive transactions operate at the highest tier with full homomorphic encryption.
The framework's design acknowledges that perfect agent safety remains challenging. Instead of pursuing an unattainable ideal, AgentCrypt provides graduated controls that balance security with operational efficiency. This pragmatic approach suits enterprises navigating evolving threat landscapes while maintaining productivity.
"AgentCrypt's layered privacy model represents a paradigm shift from binary access controls to nuanced, context-aware encryption that protects data throughout its lifecycle, even when AI systems err or face adversarial conditions."
Key AgentCrypt capabilities include:
- Four-tiered privacy framework from open exchange to homomorphic encryption
- Context-aware policy enforcement based on agent roles and data sensitivity
- Protection against privacy leaks during AI model errors or unexpected behavior
- Compliance-ready architecture supporting regulatory audit requirements
- Scalable design accommodating growing agent populations and message volumes
For enterprises requiring advanced encryption and robust compliance frameworks, AgentCrypt offers a technically sophisticated solution. Its integration with secure messaging platforms 2026 demonstrates practical applicability beyond theoretical frameworks.
BlockA2A: decentralized trust and integrity for multi-agent communication
BlockA2A takes a fundamentally different approach by eliminating centralized trust bottlenecks in agent messaging. The framework ensures message authenticity, integrity, and accountability through decentralized architecture, preventing single points of failure that attackers could exploit. This design philosophy suits enterprises prioritizing transparency and auditability in agent interactions.
The decentralized model distributes trust across multiple nodes rather than concentrating it in a central authority. When agents communicate, cryptographic verification occurs across the network, making it exponentially harder for attackers to forge messages or manipulate interactions. This architecture neutralizes prompt-based attacks and communication exploits that plague centralized systems.
Accountability mechanisms in BlockA2A provide comprehensive audit trails for every agent interaction. You can trace message origins, verify delivery, and reconstruct communication sequences for compliance reporting or incident investigation. These capabilities prove essential for regulated industries where demonstrating data handling practices is mandatory.
Empirical testing shows BlockA2A's robustness against behavioral and systemic attacks on multi-agent systems. The framework withstands attempts to compromise individual agents, manipulate message flows, or exploit trust relationships. Its resilience stems from the distributed verification model that requires consensus across multiple nodes before accepting any communication as valid.
BlockA2A excels in scenarios requiring trustless operation. When your enterprise cannot rely on a single trusted authority or when regulatory requirements mandate distributed control, this framework provides technical solutions. The transparency inherent in its design also supports forensic analysis and regulatory audits more effectively than opaque centralized systems.
Pro Tip: Consider BlockA2A when your compliance framework requires immutable audit trails and when your threat model includes insider risks or compromised central authorities. The decentralized architecture provides defense in depth that centralized solutions cannot match.
BlockA2A distinguishes itself through:
- Elimination of centralized trust points vulnerable to exploitation
- Cryptographic guarantees for message authenticity and integrity
- Comprehensive accountability supporting compliance and forensics
- Proven resilience against multi-agent system attack vectors
- Transparency enabling regulatory audit and verification
For organizations exploring types of workplace messaging apps with advanced security requirements, BlockA2A offers a compelling alternative to traditional centralized architectures.
Comparing secure messaging solutions for agents: features and use cases
Understanding how AgentCrypt, BlockA2A, and traditional methods compare helps you match solutions to your specific enterprise requirements. Each approach offers distinct advantages depending on your security priorities, compliance mandates, and operational context.
| Feature | AgentCrypt | BlockA2A | Traditional Methods |
|---|---|---|---|
| Encryption depth | Four-tiered including homomorphic | Standard encryption in transit/rest | Basic encryption, often binary |
| Trust model | Centralized with layered policies | Fully decentralized consensus | Centralized authority |
| Privacy during computation | Yes, via homomorphic encryption | Limited to message transport | No, data decrypted for processing |
| Attack resilience | High against model errors and leaks | High against systemic and behavioral attacks | Vulnerable to post-access risks |
| Compliance support | Strong, with granular policy controls | Strong, with immutable audit trails | Moderate, limited accountability |
| Deployment complexity | Moderate to high | High, requires distributed infrastructure | Low to moderate |
| Scalability | High with proper infrastructure | Moderate, consensus overhead | High in centralized architectures |
AgentCrypt suits enterprises prioritizing data confidentiality during computation and requiring flexible privacy tiers. Its homomorphic encryption capabilities make it ideal for financial services, healthcare, and legal sectors where sensitive data processing occurs continuously. The framework's ability to maintain privacy even when AI models err provides crucial compliance assurance.
BlockA2A excels when trustless operation and transparent accountability are paramount. Regulated industries facing stringent audit requirements benefit from its immutable logging and distributed verification. Organizations concerned about insider threats or centralized authority compromise find its decentralized architecture compelling.
Traditional methods remain viable for less sensitive communications or legacy system integration. However, traditional access controls are insufficient for protecting against post-access privacy risks inherent in agent operations. Consider these approaches only when encryption during computation is not required and when compliance mandates are minimal.
Key decision factors include:
- Data sensitivity level and regulatory requirements
- Tolerance for centralized versus decentralized trust models
- Need for privacy during computation versus transport only
- Existing infrastructure and integration complexity
- Scalability requirements as agent populations grow
- Budget for implementation and ongoing maintenance
Your choice should align with your enterprise's risk profile and operational priorities. Evaluate each solution against your specific threat model and compliance framework. Many organizations implement hybrid approaches, using different solutions for various agent types and communication contexts. Exploring efficient team messaging steps can help you design an integrated strategy that balances security with productivity.
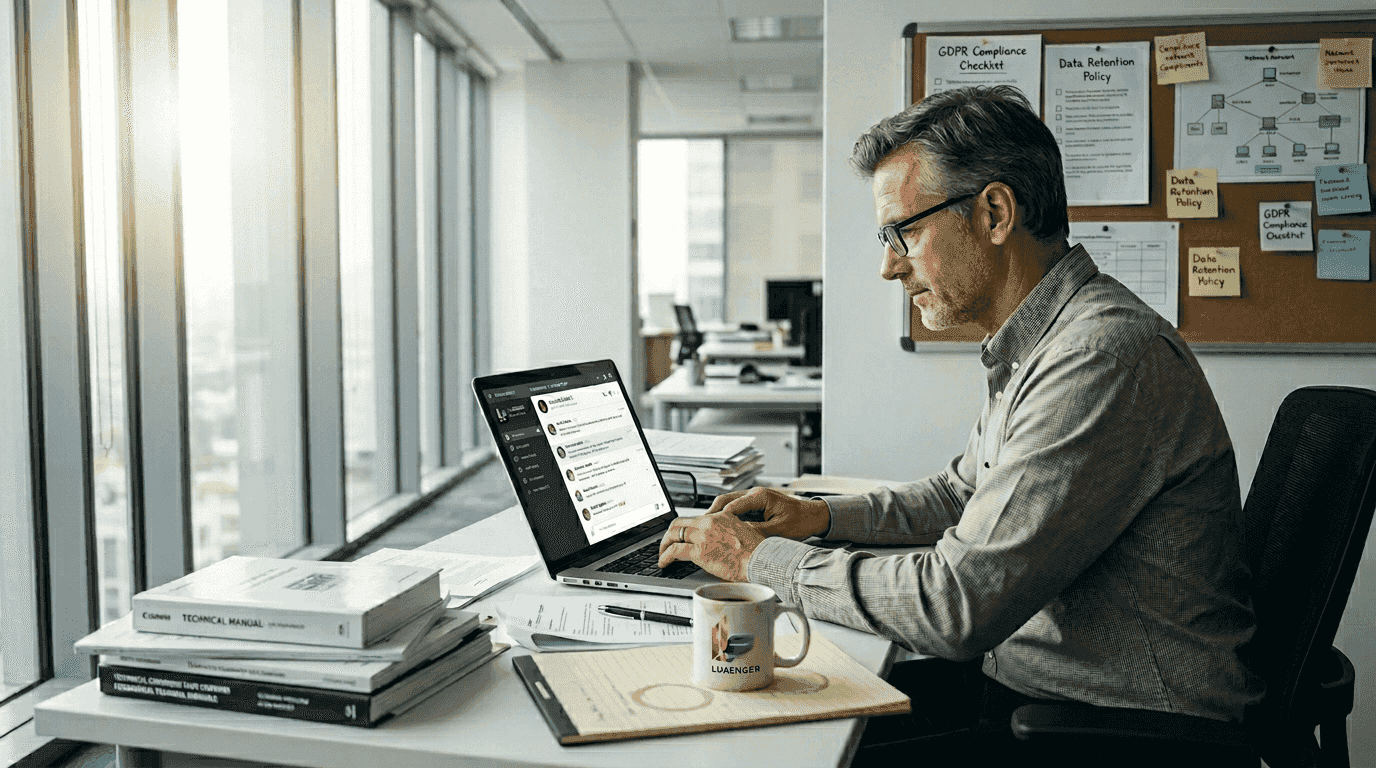
Explore Luxenger's secure messaging solutions for enterprises
Implementing the secure messaging frameworks discussed requires a platform that translates theoretical principles into practical enterprise tools. Luxenger delivers bank-grade security infrastructure specifically designed for organizations deploying AI agents and requiring robust data confidentiality. Our platform integrates layered encryption, role-based access controls, and comprehensive audit capabilities that align with the evaluation criteria outlined in this guide.
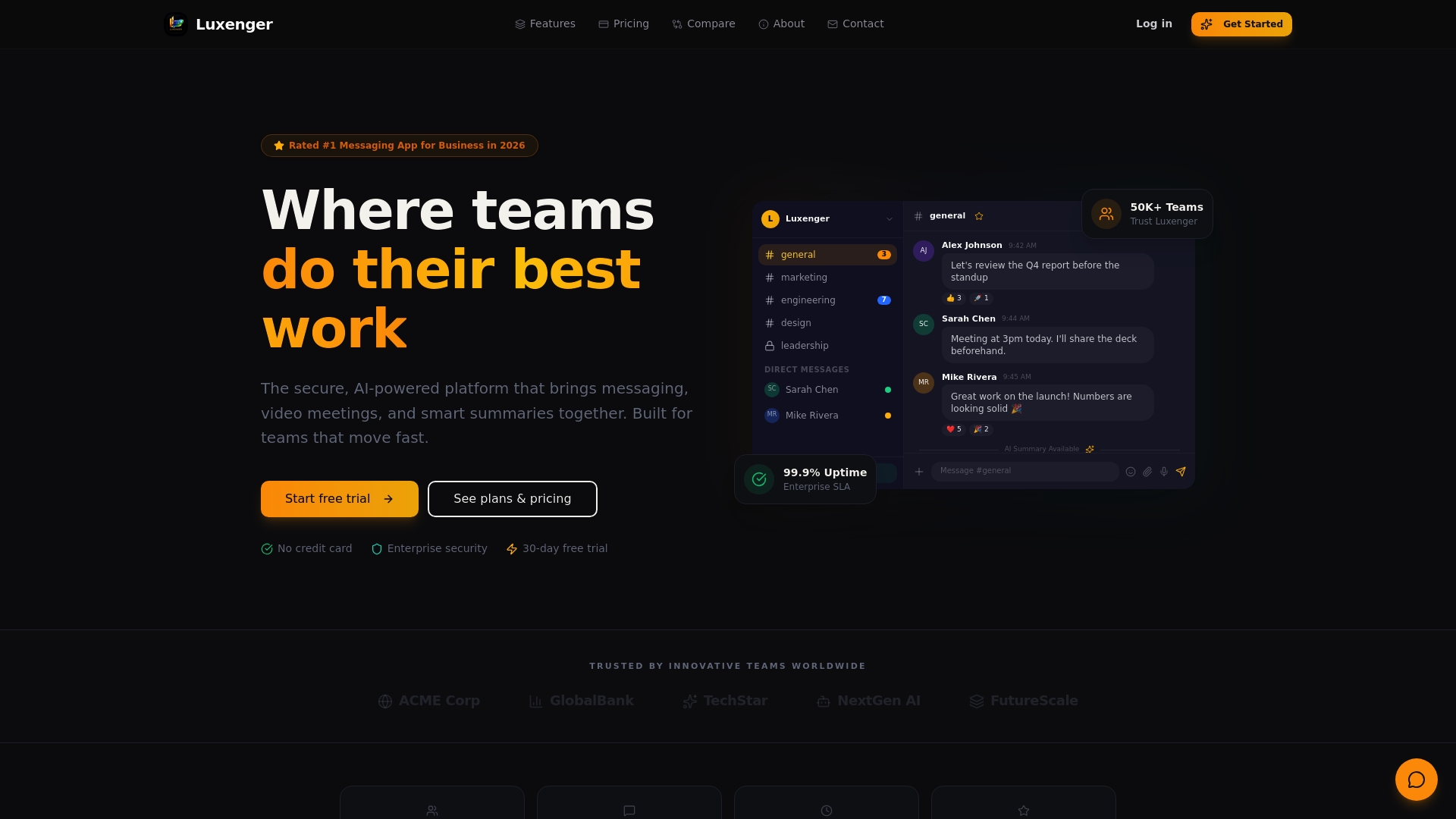
Luxenger supports the sophisticated privacy requirements of modern agent communications while maintaining the usability your teams expect. AI-powered features like conversation summaries and real-time translation enhance productivity without compromising security. Whether you need homomorphic encryption for sensitive computations or decentralized verification for compliance, our flexible architecture adapts to your specific requirements. Explore how Luxenger enterprise operations can secure your agent messaging infrastructure, review our pricing options, and discover comprehensive enterprise messaging security best practices to guide your implementation.
Frequently asked questions
What is secure messaging for agents?
Secure messaging for agents refers to communication infrastructure designed specifically for AI or software agents handling sensitive enterprise data. Unlike traditional messaging focused on human users, agent messaging must address unique challenges like privacy during computation, protection against algorithmic errors, and accountability across autonomous interactions. These systems implement layered encryption, fine-grained access controls, and integrity guarantees that prevent data exposure even when agents process information or collaborate without human oversight.
How does AgentCrypt enhance data privacy in agent communications?
AgentCrypt applies a four-tiered encryption framework ranging from open data exchange to fully homomorphic computation. This layered approach lets you match privacy controls precisely to each communication context and data sensitivity level. The framework's most powerful capability is enabling computation on encrypted data, meaning agents can process sensitive information without ever decrypting it. Privacy protections remain effective even when AI models make errors or behave unexpectedly, providing robust compliance assurance across diverse operational scenarios.
What makes BlockA2A effective against agent communication attacks?
BlockA2A eliminates centralized trust points that attackers could exploit, instead distributing verification across a decentralized network. This architecture ensures message authenticity, integrity, and accountability through cryptographic consensus rather than reliance on a single authority. The framework neutralizes prompt injection attacks, behavioral manipulation, and systemic exploits by requiring distributed validation before accepting any communication as legitimate. Comprehensive audit trails support forensic investigation and regulatory compliance while maintaining operational transparency.
How can IT managers choose the best secure messaging solution for their teams?
Start by evaluating your data privacy needs beyond simple binary access controls. Consider whether you require privacy during computation, which demands homomorphic encryption capabilities like those in AgentCrypt. Assess your tolerance for centralized versus decentralized trust models based on your threat profile and compliance requirements. Compare encryption levels, auditability features, and attack resilience across solutions. Match these technical capabilities to your enterprise's specific regulatory mandates, existing infrastructure, and scalability requirements. Review enterprise messaging security best practices to ensure your chosen solution aligns with industry standards and supports your long-term security strategy.