Many enterprises assume their internal messaging platforms are secure by default, yet data breaches often result from overlooked security gaps in these very systems. The reality is that protecting sensitive communications requires deliberate strategy, advanced technologies, and continuous vigilance. This guide reveals the critical security measures you need to safeguard your organization's internal messaging, from foundational encryption principles to AI-enhanced threat detection. You'll discover how to evaluate platform security features, implement robust protection protocols, and maintain compliance while enabling seamless team collaboration.
Table of Contents
- Key takeaways
- Common misconceptions about data security in enterprise messaging
- Fundamental principles and technologies underpinning secure enterprise messaging
- Comparing security features in leading enterprise messaging platforms
- Implementing and maintaining secure enterprise messaging practices
- Explore Luxenger's secure messaging solutions
- Frequently asked questions about data security in enterprise messaging
Key Takeaways
| Point | Details |
|---|---|
| End to end encryption | End to end encryption protects message confidentiality across the entire lifecycle. |
| Multifactor authentication | Multifactor authentication significantly reduces unauthorized access even when passwords are compromised. |
| Platform security evaluation | Regularly assess encryption models, access controls, and regulatory compliance to reduce risk. |
| AI for threat detection | Integrating artificial intelligence can improve threat detection and help manage messages more securely. |
Common misconceptions about data security in enterprise messaging
The assumption that popular messaging platforms automatically provide adequate security creates dangerous blind spots. Many IT managers believe that simply deploying a recognized brand guarantees protection, but platform popularity doesn't equal comprehensive security. Each tool offers different encryption models, access controls, and compliance capabilities.
User behavior represents the weakest link in most security chains. Phishing attacks, credential sharing, and poor password hygiene compromise even the most secure platforms. Attackers increasingly target employees through social engineering rather than attempting direct technical exploits. A single compromised account can expose entire conversation histories, shared files, and organizational intelligence.
Compliance awareness gaps compound these risks. Organizations in healthcare, finance, and legal sectors face strict regulations around data handling, yet many teams use messaging tools without verifying enterprise messaging security best practices or regulatory alignment. The consequences extend beyond fines to include reputational damage and loss of client trust.
High-profile breaches illustrate these vulnerabilities clearly:
- A financial services firm lost client data when employees used unauthorized messaging apps for convenience
- Healthcare providers faced HIPAA violations after patient information leaked through unencrypted channels
- Legal teams exposed privileged communications by failing to enable proper access controls
- Technology companies suffered intellectual property theft through compromised messaging accounts
These incidents share common threads: underestimating risk, prioritizing convenience over security, and lacking comprehensive security protocols.
"The greatest security risk isn't the technology itself, but the assumption that default settings provide adequate protection. Every enterprise messaging deployment requires intentional security configuration and ongoing monitoring."
Recognizing these misconceptions creates the foundation for implementing genuinely secure messaging practices. Understanding what doesn't work clarifies what does.
Fundamental principles and technologies underpinning secure enterprise messaging
End-to-end encryption is critical for ensuring message confidentiality in enterprise communications. E2EE ensures only intended recipients can decrypt messages, preventing interception during transmission or storage. Unlike transport encryption that protects data only while moving between servers, E2EE maintains protection throughout the entire message lifecycle. This distinction matters enormously when handling confidential business information, trade secrets, or personal data.

Authentication mechanisms verify user identities before granting access. Multi-factor authentication (MFA) requires multiple verification methods, typically combining something you know (password), something you have (mobile device), and sometimes something you are (biometric data). MFA dramatically reduces unauthorized access risks, even when passwords are compromised. Single sign-on (SSO) integration with corporate identity providers streamlines access while maintaining security standards.
Compliance with industry standards like HIPAA and GDPR mandates specific security controls for messaging platforms. These frameworks require data encryption, access logging, retention policies, and breach notification procedures. Organizations must verify that messaging solutions support required compliance features before deployment.
| Technology | Security benefit | Implementation consideration |
|---|---|---|
| End-to-end encryption | Prevents message interception and unauthorized access | Verify encryption extends to file sharing and voice communications |
| Multi-factor authentication | Blocks 99.9% of automated credential attacks | Integrate with existing identity management systems |
| Zero-knowledge architecture | Platform providers cannot access message content | May limit some administrative capabilities |
| Perfect forward secrecy | Compromised keys don't expose past communications | Requires regular key rotation protocols |
| Secure key management | Protects encryption keys from theft or misuse | Implement hardware security modules for key storage |
Secure protocols establish trusted communication channels. TLS 1.3 provides transport security, while protocols like Signal Protocol offer proven E2EE implementations. Platform architecture matters too: centralized systems create single points of failure, while federated or decentralized models distribute risk.
Pro Tip: Schedule quarterly reviews of your messaging platform's audit logs to identify unusual access patterns, failed login attempts, or suspicious file transfers. Early detection of anomalies prevents minor security incidents from becoming major breaches.
Data residency controls determine where information is stored geographically, addressing both compliance requirements and data sovereignty concerns. Organizations handling European citizen data must ensure GDPR-compliant storage locations. Similar requirements exist for healthcare data, financial records, and government communications.
These foundational technologies work together to create layered security. No single measure provides complete protection, but combining encryption, authentication, compliance controls, and secure protocols builds robust defense against diverse threats.

Comparing security features in leading enterprise messaging platforms
Evaluating platforms requires examining specific security capabilities rather than accepting marketing claims. Selecting platforms with integrated security dashboards enhances real-time monitoring capabilities and simplifies compliance reporting. The differences between solutions become apparent when comparing concrete features.
| Platform capability | Essential features | Advanced features | Impact on security posture |
|---|---|---|---|
| Encryption coverage | E2EE for messages | E2EE for files, voice, video, screen sharing | Comprehensive encryption prevents data exposure across all communication types |
| Access controls | Role-based permissions | Granular channel controls, guest access limits, device management | Precise access management reduces insider threat risks |
| Audit and compliance | Basic activity logs | Real-time alerts, exportable audit trails, retention policies | Detailed logging supports incident investigation and regulatory compliance |
| Threat detection | Manual monitoring | AI-powered anomaly detection, automated threat response | Proactive identification stops attacks before damage occurs |
| Data governance | Standard retention | Custom policies, legal hold, e-discovery support | Flexible governance meets diverse regulatory requirements |
Integration capabilities determine how well messaging security aligns with broader IT infrastructure:
- SIEM integration enables centralized security monitoring across all enterprise systems
- Identity and access management (IAM) connections ensure consistent authentication policies
- Data loss prevention (DLP) tools scan messages for sensitive information before transmission
- Mobile device management (MDM) enforces security policies on smartphones and tablets
- API access allows custom security automations and workflow integrations
Platform transparency affects trust and verification. Open-source solutions enable independent security audits, while proprietary systems require trusting vendor claims. Third-party security certifications (SOC 2, ISO 27001) provide external validation of security practices.
Pro Tip: Request detailed security architecture documentation during platform evaluation. Vendors serious about security provide comprehensive technical specifications, encryption implementation details, and infrastructure diagrams. Vague responses or reluctance to share architectural information signals potential security weaknesses.
Recovery capabilities matter as much as prevention. Platforms should support secure backup and restoration without compromising encryption. Disaster recovery procedures must maintain security standards even during crisis situations. Some solutions offer immutable backups that prevent ransomware encryption.
Cost considerations extend beyond licensing fees. Platforms requiring extensive custom security development increase total ownership costs. Solutions with secure messaging platforms features built in reduce implementation time and ongoing maintenance burden. However, the cheapest option rarely provides adequate security for enterprise needs.
User experience impacts security adoption. Overly complex security measures encourage workarounds and shadow IT usage. The best platforms balance robust protection with intuitive interfaces that employees actually use correctly. Security that frustrates users ultimately fails.
Implementing and maintaining secure enterprise messaging practices
Successful deployment follows a structured approach that addresses technical, organizational, and human factors. Rushing implementation creates security gaps, while overly cautious approaches delay necessary protections.
- Conduct comprehensive requirements analysis examining regulatory obligations, data sensitivity levels, integration needs, and user workflows
- Evaluate platforms against specific security criteria using proof-of-concept testing with real use cases and security scenarios
- Design architecture integrating messaging security with existing identity management, network security, and compliance systems
- Configure security settings enabling all relevant protections before user onboarding, including encryption, MFA, and access controls
- Develop security policies documenting acceptable use, data handling procedures, incident response protocols, and compliance requirements
- Execute phased rollout starting with security-conscious pilot groups before expanding to entire organization
- Deliver comprehensive training covering security features, threat awareness, proper usage procedures, and reporting mechanisms
- Establish monitoring processes tracking security metrics, audit logs, compliance status, and user adoption patterns
Continuous employee training and periodic security assessments reduce messaging-related vulnerabilities throughout the platform lifecycle. Initial training addresses basic security practices, while ongoing education covers emerging threats, new features, and lessons from security incidents.
Ongoing maintenance tasks preserve security effectiveness:
- Apply security updates and patches within 48 hours of release to close known vulnerabilities
- Review access permissions quarterly, removing unnecessary privileges and inactive accounts
- Conduct annual security assessments testing encryption implementation, access controls, and incident response
- Monitor threat intelligence feeds for messaging platform vulnerabilities and attack techniques
- Test disaster recovery procedures semi-annually to verify backup integrity and restoration capabilities
- Audit third-party integrations for security risks and unnecessary data access
- Update security policies as regulations evolve and business requirements change
Common implementation pitfalls to avoid:
- Deploying platforms with default settings instead of hardening configurations
- Granting excessive administrative privileges to too many users
- Neglecting mobile security policies for smartphone and tablet access
- Failing to disable legacy authentication methods that bypass MFA
- Overlooking file sharing security when focusing only on message encryption
- Ignoring integration security between messaging and other business systems
- Skipping security training for executive leadership who handle sensitive information
Incident response planning prepares organizations for security events. Procedures should define detection methods, containment steps, investigation processes, communication protocols, and recovery actions. Regular tabletop exercises test response capabilities without waiting for actual incidents.
Compliance monitoring verifies ongoing adherence to regulatory requirements. Automated tools can flag potential violations like unauthorized data sharing or retention policy breaches. Regular compliance audits identify gaps before regulators do. Documentation of security measures and policy enforcement supports compliance demonstrations.
Success metrics track security program effectiveness. Monitor failed login attempts, policy violations, security training completion rates, incident response times, and audit finding remediation. These measurements identify improvement opportunities and demonstrate security investment value to leadership.
Explore Luxenger's secure messaging solutions
Implementing these security practices becomes significantly easier with platforms designed for enterprise security from the ground up. Luxenger enterprise messaging combines bank-grade encryption with AI-powered communication enhancements, delivering both security and productivity. The platform's comprehensive feature set includes end-to-end encryption across messages, files, and voice communications, integrated threat detection, and detailed audit capabilities.
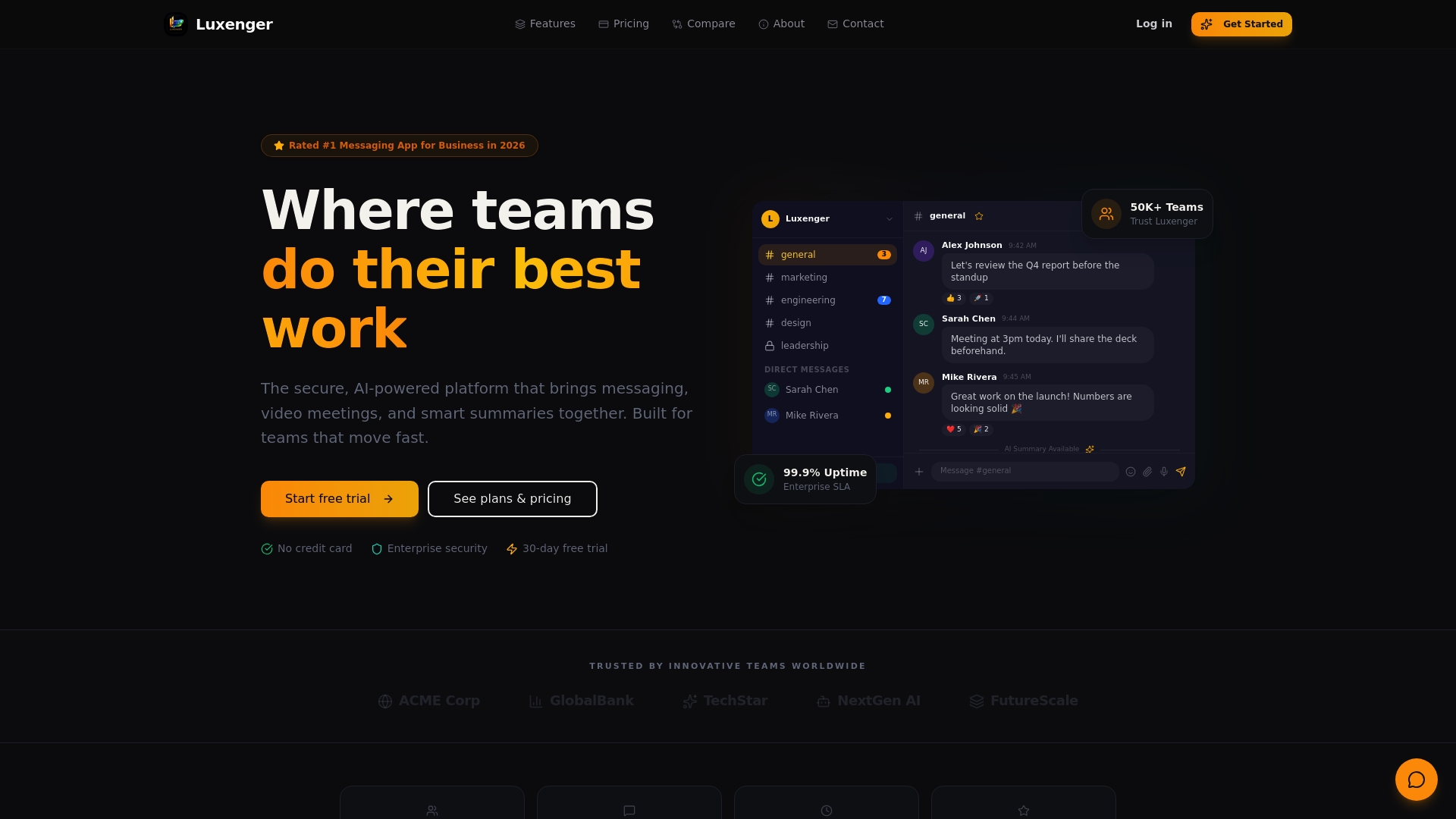
The security dashboard provides real-time visibility into access patterns, security events, and compliance status, enabling proactive risk management. AI-powered summaries and real-time translation enhance team collaboration without compromising data protection. For organizations seeking alternatives to legacy platforms that balance advanced capabilities with rigorous security standards, Luxenger offers a proven solution trusted by enterprises across regulated industries.
Frequently asked questions about data security in enterprise messaging
What makes a messaging platform secure?
A secure messaging platform implements end-to-end encryption for all communication types, enforces multi-factor authentication, provides granular access controls, maintains comprehensive audit logs, and supports relevant compliance frameworks. The platform architecture should prevent even service providers from accessing message content. Regular security updates and transparent security practices are equally important.
How does AI improve messaging security?
AI analyzes communication patterns to detect anomalies indicating potential security threats, such as unusual login locations, abnormal message volumes, or suspicious file sharing. Machine learning models identify phishing attempts, malware distribution, and compromised accounts faster than manual monitoring. AI also automates threat response, blocking suspicious activities before they cause damage.
Can secure messaging meet compliance requirements?
Yes, enterprise messaging platforms designed for regulated industries include features specifically supporting HIPAA, GDPR, SOC 2, and other compliance frameworks. These features include data encryption, access controls, audit trails, retention policies, and e-discovery capabilities. Organizations must verify that chosen platforms support their specific regulatory requirements and properly configure compliance features.
What are best practices for employee training?
Effective training combines initial onboarding covering platform security features with ongoing education addressing emerging threats and policy updates. Use realistic scenarios demonstrating phishing attempts, social engineering tactics, and proper data handling. Make training interactive rather than lecture-based, test comprehension through simulations, and provide quick-reference guides for common security tasks. Executive leadership should receive specialized training on handling highly sensitive communications.
How to handle a security breach in messaging systems?
Immediate containment involves disabling compromised accounts, rotating potentially exposed credentials, and isolating affected systems. Investigate the breach scope by reviewing audit logs to identify accessed data and attack methods. Notify affected parties and regulators according to legal requirements and timelines. Implement corrective measures addressing the root cause, then conduct post-incident analysis to prevent recurrence. Document all actions for compliance and improvement purposes.
