TL;DR:
- Modern encrypted messaging apps deliver near-zero latency with minimal device overhead.
- Endpoint-local AI preserves security and confidentiality without sacrificing functionality.
- Proper threat modeling and platform selection are essential for secure, scalable enterprise messaging.
Performance benchmarks confirm that modern encrypted messaging apps carry virtually no latency overhead even at enterprise scale, yet IT managers still hesitate to deploy them. The assumption that strong encryption means slower communication, drained batteries, or frustrated employees is simply not supported by evidence. Today's enterprise-grade platforms have solved the performance problem. What remains is helping your team understand what actually works, what the real risks are, and how to deploy secure messaging without compromising speed, scalability, or the AI-powered features your organization increasingly depends on. This guide gives you that clarity.
Table of Contents
- Demystifying encrypted business messaging: What actually works
- Performance, scalability, and security: Enterprise benchmarks explained
- AI integration: Balancing innovation and confidentiality
- Deployment challenges and practical strategies for enterprise adoption
- A fresh take: What most enterprise leaders misunderstand about encrypted business messaging
- How Luxenger helps you achieve secure, scalable enterprise messaging
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Enterprise-grade efficiency | Modern encrypted messaging apps operate with minimal latency and negligible device resource usage. |
| AI integration risks | Endpoint-local AI protects confidentiality, while server-side AI may compromise encrypted chats. |
| Group management nuance | Protocols like MLS are efficient for large, trusted teams but require careful handling of authentication and metadata. |
| Deployment best practices | Prioritize platforms that minimize metadata exposure and streamline secure device linking for enterprise rollouts. |
| Scalable, actionable solutions | Reliable encrypted messaging platforms are ready for secure, scalable enterprise adoption without major trade-offs. |
Demystifying encrypted business messaging: What actually works
End-to-end encryption (E2EE) means that messages are encrypted on the sender's device and can only be decrypted by the intended recipient. No server in the middle can read the content. Not the platform provider, not a cloud vendor, and not a threat actor who intercepts traffic. This is the foundational guarantee that makes E2EE the gold standard for enterprise messaging.
The common misconception is that this level of protection comes at a steep performance cost. It does not. Platforms like Signal, Wire, and Element deliver efficient encrypted messaging with minimal device overhead, even when handling large group conversations or frequent message bursts. The cryptographic operations involved are lightweight on modern hardware.
Here is what enterprise-grade encrypted messaging actually delivers when implemented correctly:
- End-to-end encryption for all message types, including files, images, and voice
- Group messaging with key management that handles member changes without breaking security
- Multi-device synchronization so employees can switch between laptop, phone, and tablet seamlessly
- Compliance logging that captures metadata without exposing message content
- Identity verification to prevent impersonation within your organization
Understanding these capabilities is the first step. If you want a deeper look at how these protections apply in practice, our secure messaging guide covers the technical foundations in detail. For a broader view of how different platforms compare, see our breakdown of types of workplace messaging apps.
Pro Tip: When evaluating platforms, ask vendors specifically how they handle key management during group membership changes. This is where many solutions cut corners and where your security posture is most vulnerable.
The battery drain myth also deserves a direct response. Encryption processing is handled by dedicated hardware acceleration on virtually every modern mobile chip. The overhead is negligible compared to rendering a video thumbnail or loading an attachment preview. Security is not the bottleneck.
Performance, scalability, and security: Enterprise benchmarks explained
Numbers matter when you are making a platform decision for thousands of employees. Benchmark data gives IT decision-makers the evidence they need to push back against vague vendor claims.
In comparative testing, Wire's key exchange is 39% faster than Signal under low-bandwidth conditions, while Element shows higher round-trip time (RTT) but maintains low idle CPU usage. RTT measures the time from message send to delivery confirmation. Low idle CPU means the app is not quietly draining resources when employees are not actively messaging.

| Platform | Key exchange speed | Idle CPU usage | RTT under load |
|---|---|---|---|
| Signal | Baseline | Very low | Low |
| Wire | 39% faster than Signal | Very low | Low |
| Element | Moderate | Low | Higher than Signal |
These differences matter in specific scenarios. If your workforce operates in areas with unreliable connectivity, Wire's faster key exchange becomes a real operational advantage. If you are running a global deployment where servers are geographically distributed, Element's RTT characteristics are worth factoring into your architecture decisions.
The Messaging Layer Security (MLS) protocol is worth understanding here. MLS enables O(log n) group key rekeying for large groups, meaning the work required to rekey when someone joins or leaves a group scales logarithmically rather than linearly. For a group of 1,000 employees, this is a significant efficiency gain. However, MLS has been criticized for requiring trust in authentication services, which introduces a dependency that some security teams find uncomfortable.
"The efficiency gains from MLS are real, but so is the trust requirement. For enterprise environments with controlled identity management, this is a manageable trade-off. For open or federated deployments, it requires careful evaluation."
Metadata is the other dimension that benchmarks rarely capture. Even with perfect E2EE, metadata reveals who is communicating with whom, when, and in what group configuration. This is sensitive information in enterprise contexts, particularly for legal, finance, and executive teams. Our guide on enterprise chat security addresses metadata risks in detail. For a feature-level comparison, see our analysis of secure messaging platform features.

AI integration: Balancing innovation and confidentiality
AI features are now a baseline expectation for enterprise messaging platforms. Conversation summaries, smart search, translation, and sentiment analysis all add genuine productivity value. The problem is that most AI processing models assume access to plaintext data, which is fundamentally incompatible with E2EE.
When AI runs on a server, it needs to read the message content. If your messages are end-to-end encrypted, the server cannot read them without breaking the encryption. This means server-side AI risks breaking E2EE confidentiality unless the AI is performed directly on the endpoint device.
Here is what that means in practice:
- Endpoint-local AI processes data on the user's device, preserving E2EE guarantees entirely
- Server-side AI requires decryption at the server, which eliminates the core security promise
- Hybrid approaches may process only metadata or anonymized signals, but these still carry metadata exposure risks
- Training on encrypted data is not currently feasible without breaking encryption, so any AI that learns from your conversations is doing so on plaintext
Pro Tip: Before enabling any AI feature in your messaging platform, ask the vendor a direct question: where does the AI processing happen? If the answer is "our servers" or "the cloud," your E2EE guarantee is conditional at best.
The practical implication for IT managers is straightforward. Prioritize platforms that run AI features locally. This is technically harder to build, which is why fewer vendors offer it, but it is the only approach that maintains genuine confidentiality. Our article on secure AI collaboration explores how forward-thinking enterprises are navigating this trade-off without sacrificing either innovation or security.
Deployment challenges and practical strategies for enterprise adoption
Knowing the right platform is only half the work. Deployment is where most enterprise rollouts encounter friction. The edge cases around metadata, device sync, and group key management are where security guarantees can quietly erode.
Metadata exposure and secure device linking present distinct challenges depending on the protocol you choose. Signal's Sealed Sender feature hides the sender's identity from the server, reducing metadata exposure significantly. MLS uses a tree-based structure for group key management, which is efficient but requires a trusted authentication service to function correctly.
| Feature | Signal (Sealed Sender) | Element (MLS) |
|---|---|---|
| Metadata exposure | Minimized via Sealed Sender | Moderate, depends on server config |
| Group rekeying efficiency | Linear scaling | O(log n) scaling |
| Trust requirement | Minimal | Authentication service required |
| Enterprise key management | Limited native tooling | More enterprise controls available |
Here is a practical deployment process for enterprise teams:
- Audit your threat model before selecting a platform. Identify what data is most sensitive and who the realistic adversaries are.
- Evaluate metadata policies for each platform under consideration. Request documentation, not just marketing claims.
- Test multi-device sync in a controlled environment with a representative sample of your device fleet.
- Configure group management policies before rollout. Decide who can create groups, add members, and how departures are handled.
- Train IT staff on key management so they can respond to device loss or employee offboarding without creating security gaps.
- Establish an incident response protocol specific to messaging, including what to do if a device is compromised.
Pro Tip: Prioritize platforms with enterprise-focused group management and minimal metadata exposure from day one. Retrofitting security controls after a large-scale deployment is significantly harder and more expensive than building them in at the start.
For a structured approach to rolling this out, our guide on secure messaging workflow provides a step-by-step framework. You can also review modern messaging app features to benchmark what your current tools may be missing.
A fresh take: What most enterprise leaders misunderstand about encrypted business messaging
Here is the uncomfortable reality: most enterprise leaders frame secure messaging as a trade-off. Security versus speed. Encryption versus AI features. Compliance versus usability. This framing is outdated and it is leading to bad decisions.
The data does not support the trade-off narrative. Performance benchmarks confirm that encryption overhead is negligible. Endpoint-local AI preserves confidentiality without sacrificing functionality. The tools exist to have both.
What leaders actually need to reconsider is where they place their trust. MLS is brilliant for enterprise control but problematic for large untrusted public groups. In a controlled enterprise environment with managed identity, MLS is a strong choice. In a federated or open deployment, the trust assumptions become liabilities.
The real gap is not technical. It is organizational. Most enterprises have not defined their threat model clearly enough to make an informed platform choice. They pick a tool based on familiarity or vendor relationships, then try to bolt security on afterward. That approach consistently underperforms.
If you want messaging that is genuinely secure and scalable, start with the threat model, choose the protocol that fits your trust environment, and then select the platform. The technology is ready. The question is whether your organization is ready to use it correctly.
How Luxenger helps you achieve secure, scalable enterprise messaging
Everything covered in this article points to one conclusion: enterprise messaging security is achievable without sacrificing performance or innovation, but only if you choose the right platform from the start.
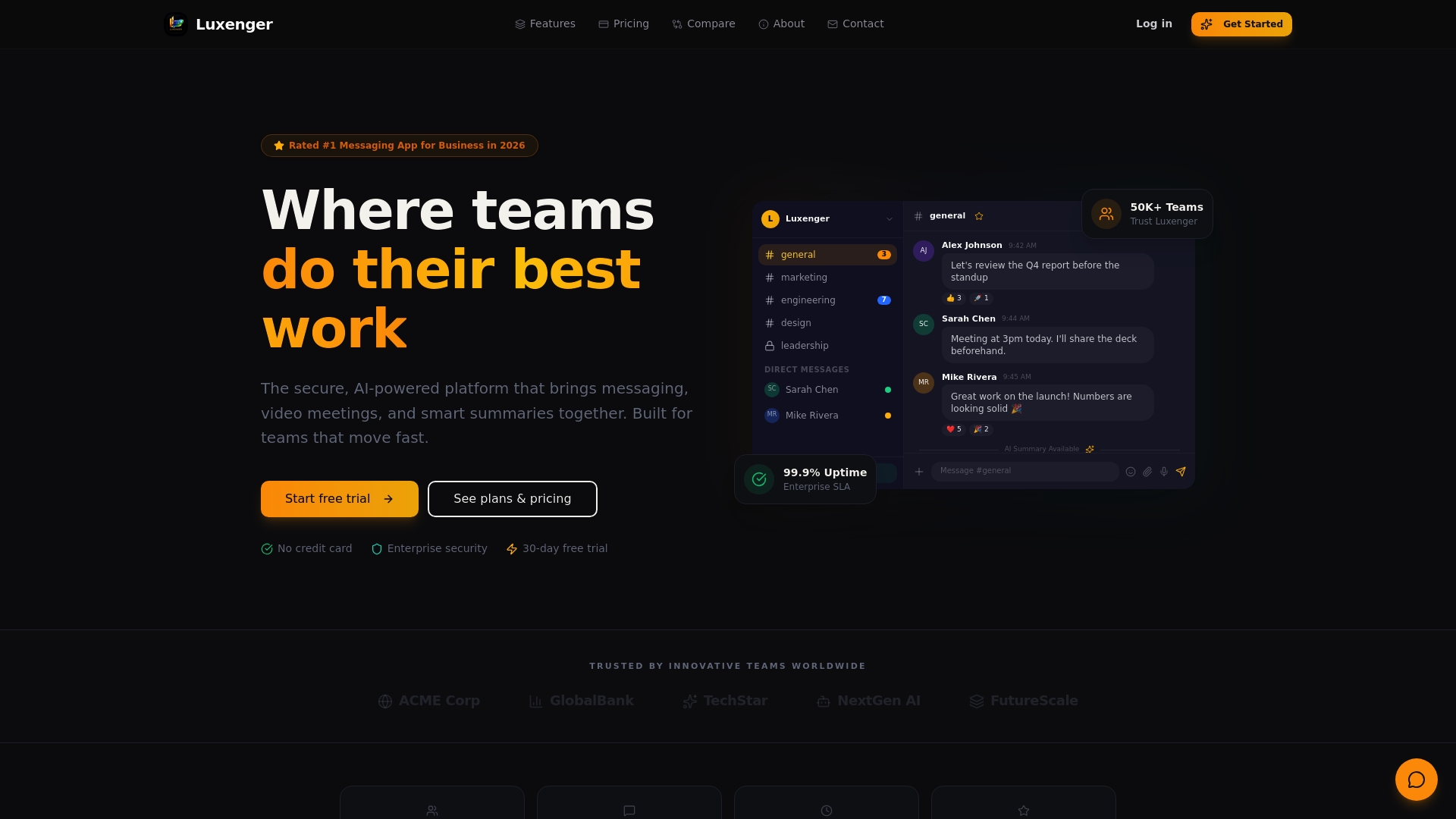
Luxenger for enterprise operations is built specifically for organizations that cannot afford to compromise on either security or capability. With bank-grade encryption, endpoint-local AI features including conversation summaries and real-time translation, and enterprise-grade group management, Luxenger addresses the exact challenges outlined here. As a purpose-built enterprise messaging platform, it removes the trade-off between innovation and confidentiality. Review pricing to find the plan that fits your organization's scale and security requirements.
Frequently asked questions
What is end-to-end encryption and why does it matter for business messaging?
End-to-end encryption ensures only the sender and receiver can access message content, protecting confidentiality even from the platform's own servers. For enterprises, this means sensitive communications cannot be intercepted, subpoenaed from a vendor, or exposed in a server breach.
Can AI be safely used with encrypted business messaging?
AI features are safe when processed locally on endpoints. Server-side AI processing requires decrypting messages at the server level, which breaks E2EE guarantees and exposes plaintext to the platform provider.
Does implementing encrypted messaging slow down team communications?
Performance benchmarks confirm that modern encrypted messaging has minimal latency and CPU overhead even at enterprise scale, making the performance trade-off argument largely obsolete for current hardware.
How do encrypted group chats handle join and leave events securely?
MLS uses O(log n) rekeying for efficient group key updates but requires trust in an authentication service, while Signal's approach minimizes metadata exposure with a different set of trade-offs.
