TL;DR:
- Implement phishing-resistant MFA using hardware tokens or certificate-based authentication for strong access control.
- Use Data Loss Prevention tools to monitor and block sensitive data from leaving enterprise messaging platforms.
- Restrict external access and thoroughly audit messaging activities to prevent breaches and ensure compliance.
A single exposed chat thread can trigger a regulatory investigation, cost millions in fines, and permanently damage your organization's reputation. Enterprise messaging platforms carry sensitive data every minute: contract terms, personnel decisions, financial projections, and customer records. Yet many security teams still rely on default platform settings and hope for the best. That approach is no longer viable. Compliance mandates like HIPAA, SOX, and GDPR demand provable controls, and threat actors specifically target messaging tools because they are always on and often under-monitored. This checklist walks you through five critical security controls every enterprise must implement to protect internal communications and stay ahead of evolving threats.
Table of Contents
- 1. Enforce phishing-resistant MFA for all users
- 2. Implement Data Loss Prevention (DLP) for messages and files
- 3. Restrict external access and control integrations
- 4. Monitor, log, and regularly audit all messaging activities
- 5. Harden platforms: baselines, mobile controls, and session policies
- A practical security checklist is only the start
- Ready to secure your messaging environment?
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Phishing-resistant MFA | Protects all user access using methods attackers can't easily bypass like FIDO2 or hardware tokens. |
| DLP blocks leaks | Monitors and automatically stops sensitive data from leaving your messaging environment. |
| Control external risk | Restrict external access and all third-party integrations to minimize exposure. |
| Monitor continuously | Enable full logging and recurring audits so threats are detected quickly. |
| Harden every layer | Apply security baselines and mobile management to protect devices, software, and infrastructure. |
1. Enforce phishing-resistant MFA for all users
Access control is your first and most important line of defense. If an attacker can steal a password and walk straight into your messaging environment, every other control you build becomes irrelevant. Multi-factor authentication (MFA) adds a second verification step, but not all MFA is equal. SMS-based codes, for example, are vulnerable to SIM-swapping attacks where a threat actor convinces a carrier to transfer your phone number to their device. That one gap can bypass what most people assume is solid protection.
Phishing-resistant MFA eliminates that weakness. The CISA SCuBA baseline mandates phishing-resistant MFA for Microsoft 365, including Teams, specifically requiring FIDO2 security keys, hardware tokens, or certificate-based authentication. These methods cryptographically bind the authentication to the legitimate site, so a fake login page simply cannot capture a usable credential.
When rolling out phishing-resistant MFA across your enterprise, focus on these options:
- FIDO2 security keys (YubiKey, Google Titan): the gold standard for phishing resistance
- Certificate-based authentication: ideal for managed devices already enrolled in your PKI
- Hardware tokens with TOTP: a strong fallback where FIDO2 is not yet supported
- Conditional Access policies: enforce MFA at the platform level for Microsoft Teams, Google Workspace, and Slack
Don't overlook bot and API accounts. These service accounts often carry broad permissions and are rarely reviewed. Apply least privilege principles and rotate credentials on a defined schedule. For a deeper look at how MFA fits into broader secure messaging workflow steps, it pays to map authentication controls to each data flow in your environment.
"Phishing-resistant MFA is not a nice-to-have. It is the baseline expectation for any organization handling regulated data in a cloud messaging environment."
Pro Tip: Automate MFA enrollment using your identity provider's bulk provisioning tools, and schedule quarterly reviews to catch stale or misconfigured authentication methods before they become a liability.
With access control as your first line of defense, next consider content-level protections.
2. Implement Data Loss Prevention (DLP) for messages and files
Securing who gets in is critical, but you also need to control what leaves. Data Loss Prevention (DLP) scans messages, attachments, and shared files in real time, then blocks or flags content that matches sensitive data patterns. Think Social Security numbers, credit card numbers, protected health information, and proprietary intellectual property.

Google Workspace DLP for Chat blocks SSN-containing messages automatically, preventing accidental or intentional leaks before they reach unauthorized recipients. A single DLP-invoked block can be the difference between a contained incident and a reportable breach carrying six-figure regulatory fines.
Here is how to configure DLP effectively for enterprise messaging:
- Define your data taxonomy. Identify which data types are regulated (PII, PHI, financial data) and which are business-sensitive (contracts, pricing, M&A details).
- Scope your policies. Apply rules to internal channels, direct messages, and external collaborative chats. Gaps in scope are where leaks happen.
- Configure keyword and pattern matching. Use regex patterns for structured data like SSNs and card numbers, and keyword lists for unstructured sensitive content.
- Enable attachment scanning. Files are the most common exfiltration vector. Scan every attachment type, including PDFs and spreadsheets.
- Set graduated responses. Warn users for borderline content, block automatically for high-confidence matches, and alert your security team for review.
For a complete view of what DLP should cover alongside other controls, the enterprise messaging security best practices framework is a solid reference point. You should also cross-check your DLP configuration against the must-have messaging features your platform should support natively.
Pro Tip: Extend DLP rules explicitly to external collaborative chats, such as Slack Connect channels or Teams guest access spaces. These external surfaces are frequently overlooked and represent a significant exposure risk.
Now that you've secured access, controlling data flow is essential.
3. Restrict external access and control integrations
Once DLP protects sensitive content, turn to the perimeter: who and what can access your enterprise messaging ecosystem. External access controls are one of the most commonly misconfigured areas in enterprise messaging deployments. Default settings in platforms like Microsoft Teams often allow anonymous meeting join, broad federation with any external domain, and unrestricted third-party app installation.
The CISA guidance for Teams is explicit: disable anonymous meeting join, restrict federation to approved domains only, and require admin approval for external invites. These three steps alone eliminate a large class of social engineering and data exfiltration risks.
Third-party app integrations deserve equal scrutiny. Bots and connectors often request broad permissions, and users frequently approve them without reading the consent screen. Requiring admin approval for every app prevents consent phishing, where an attacker tricks a user into granting a malicious app access to their messages and files.
Here is how the major platforms compare on external access controls:
| Control | Microsoft Teams | Slack | Google Chat |
|---|---|---|---|
| Anonymous meeting join | Disable in admin center | N/A | N/A |
| External federation | Restrict to approved domains | Slack Connect approval required | Domain allowlist |
| Third-party app approval | Admin-only app catalog | App approval workflow | Marketplace admin control |
| Guest access | Conditional Access enforced | Guest channel restrictions | External sharing limits |
For a thorough walkthrough of perimeter controls, the enterprise chat security guide covers platform-specific configurations in detail.
"Zero-trust means every external connection is a potential threat until proven otherwise. Review integrations on a regular cadence, not just at onboarding."
Locking down access is only half the battle. Vigilant ongoing monitoring closes the loop.
4. Monitor, log, and regularly audit all messaging activities
Even the best preventive controls will occasionally fail. Audit logging and continuous monitoring are what allow you to detect incidents fast, contain damage, and prove compliance to regulators. Without logs, you are flying blind during an investigation.
Comprehensive audit logging for Google Chat captures message content, file actions, admin changes, and integration events. Microsoft 365 provides equivalent logging through the unified audit log, covering Teams messages, calls, and file activity. Both integrate with Security Information and Event Management (SIEM) tools, enabling centralized analysis and automated alerting.
Here is what your audit log strategy should cover:
- Message content logs: Capture sent, edited, and deleted messages for the retention period required by your compliance framework.
- File transfer logs: Record every upload, download, and share event, including external shares.
- Admin action logs: Track permission changes, policy updates, and new app approvals.
- Integration activity logs: Monitor bot and connector behavior for anomalous patterns.
- DLP violation reports: Review blocked and flagged events weekly to identify policy gaps or user behavior trends.
Retention periods vary by regulation. HIPAA requires a minimum of six years. SOX mandates seven years for financial records. Build your retention policy around the strictest applicable standard, then automate deletion at the end of the defined period to limit unnecessary data exposure.
For additional context on how logging fits into your overall messaging security best practices, aligning your log strategy with your incident response playbook is strongly recommended.
Pro Tip: Configure automated SIEM alerts for DLP violations, mass file downloads, and after-hours admin changes. These behavioral anomalies are often early indicators of insider threats or compromised accounts.
5. Harden platforms: baselines, mobile controls, and session policies
With monitoring in place, you still need to harden every layer from back-end systems to endpoints. Security baselines give you a tested, authoritative starting point. For on-premises components like Exchange Server, NIST security checklists provide configuration guidance validated against real-world threat models. For cloud services, CIS Benchmarks and DISA STIGs cover Teams, Google Workspace, and Slack.
Follow this hardening sequence:
- Apply security baselines. Use DISA STIGs for on-premises servers and CIS/NIST benchmarks for cloud messaging apps. Document every deviation and the compensating control you put in place.
- Configure session timeouts. Idle sessions are an easy target. MDM and session controls for Slack, Teams, and Google Chat should enforce timeouts of 30 minutes or less for unmanaged devices.
- Disable public and guest file sharing. Unless there is a documented business need, sharing files publicly or with unauthenticated guests should be blocked at the admin level.
- Enforce Mobile Device Management (MDM) for BYOD. Personal devices accessing enterprise messaging must meet minimum security standards: screen lock, encryption, and remote wipe capability.
- Restrict copy-paste and screenshot functions. On mobile, use app-level controls through your MDM solution to prevent data extraction via screenshots.
For a complete view of what secure messaging features your platform should support natively, cross-referencing your hardening checklist against platform capabilities helps identify gaps early.
Pro Tip: Always test baseline policy changes in a staging environment before pushing to production. A misconfigured session timeout or overly aggressive DLP rule can block legitimate workflows and push users toward unsanctioned tools.
A practical security checklist is only the start
After working through hundreds of enterprise messaging deployments, one pattern stands out clearly: most serious breaches don't happen because a team skipped a checklist item. They happen because of operational drift. A policy gets configured correctly on day one, then quietly degrades as the organization grows, staff turns over, and new integrations get added without a formal review.
The uncomfortable truth is that a completed checklist can create a false sense of security. Security is iterative. The controls that protected your environment last year may not be sufficient today, especially as threat actors specifically adapt their tactics to target messaging platforms.
There is also a real tension between security and usability. Overly strict controls don't just frustrate users; they drive behavior outside sanctioned tools. When employees find that the approved platform blocks too much, they move conversations to personal WhatsApp or email. That is a worse outcome than a slightly more permissive DLP policy on your managed platform.
The goal is secure, scalable messaging that people actually use. Build controls that are tight enough to be defensible and flexible enough to support real work. Then schedule quarterly reviews to catch drift before it becomes a breach.
Ready to secure your messaging environment?
Implementing these five controls across a fragmented stack of tools is genuinely complex. Luxenger is built to simplify that process for enterprise teams.
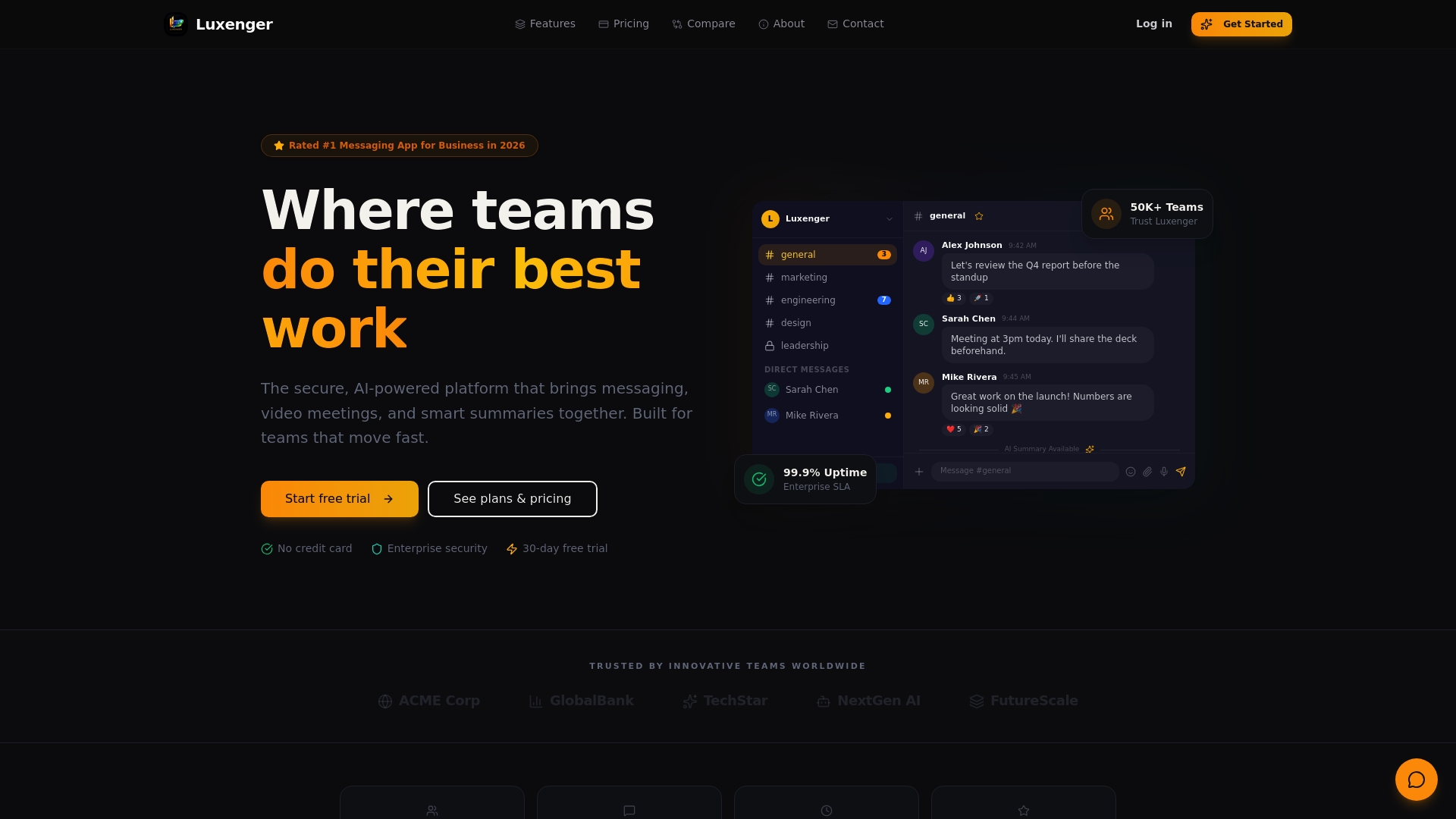
Luxenger's enterprise messaging platform delivers bank-grade security with customizable MFA, built-in DLP, admin-controlled integrations, and full audit logging out of the box. Whether you are managing a midmarket team or a global enterprise, Luxenger scales to your security requirements without sacrificing the AI-powered features and real-time collaboration your teams depend on. Explore flexible options at enterprise messaging pricing and see how Luxenger can replace your fragmented tools with one secure, auditable platform.
Frequently asked questions
What is phishing-resistant MFA, and why is it better than SMS codes?
Phishing-resistant MFA uses FIDO2 keys or hardware tokens that cryptographically bind authentication to the legitimate site, so fake login pages cannot capture usable credentials. SMS codes, by contrast, can be intercepted through SIM-swapping or real-time phishing relays.
How does DLP work in enterprise messaging apps?
DLP in Google Chat and similar platforms scans messages and file attachments for sensitive data patterns like SSNs or credit card numbers, then automatically blocks or flags them before they reach unauthorized recipients.
What should we log and monitor in messaging tools?
Audit logging for Chat should capture message content, file transfers, admin actions, and third-party app activity, then feed those logs into your SIEM for centralized analysis and automated alerting.
How do we manage BYOD security for messaging?
Use MDM for BYOD to enforce screen lock, encryption, and remote wipe on personal devices, and combine that with session timeouts and restrictions on public file sharing to limit your exposure.
