TL;DR:
- A single data breach can severely damage client trust and incur massive penalties.
- Implementing layered, Zero Trust-based messaging security reduces incidents and operational risks.
- A structured, ongoing process with specialized tools is essential for maintaining confidentiality and compliance.
One data breach can erase years of client trust overnight. For IT and communications managers at enterprises handling sensitive client interactions, the pressure to get messaging security right is not theoretical. Law firms implementing enterprise security report 73% fewer incidents and 18 to 22% insurance premium reductions, and those numbers reflect a truth every regulated industry already knows: a deliberate, layered communication process is not a luxury. This guide walks you through each stage of building and maintaining a confidential client communication workflow, from foundational tools to step-by-step execution and troubleshooting.
Table of Contents
- Understand the stakes: Why confidentiality is non-negotiable
- Build your security foundation: Essential tools and protocols
- Step-by-step confidential client communication workflow
- Troubleshooting and common mistakes: Keeping communication airtight
- Unpacking the reality: What experts get wrong about secure client communications
- Upgrade your confidential client communication process with Luxenger
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Zero Trust is foundational | Always verify user identity and device health for every confidential message or file exchange. |
| Layered security pays off | Combining encryption, access control, and monitoring reduces incidents and insurance costs. |
| Specialized platforms boost compliance | Dedicated tools make eDiscovery, audit, and redaction simpler and cheaper than generic solutions. |
| Workflow discipline minimizes risk | Clear, repeatable steps and regular audits prevent common errors and exposure. |
Understand the stakes: Why confidentiality is non-negotiable
Before designing any secure workflow, your team needs a clear-eyed view of what goes wrong and how fast. A single misconfigured permission, an unencrypted file transfer, or an employee using a personal device on a client channel can trigger consequences that take years to resolve. The financial penalties alone are staggering, but the reputational damage is often worse.
Understanding confidential messaging importance for your enterprise means recognizing three layers of risk: regulatory, financial, and operational. On the regulatory side, frameworks like HIPAA, GDPR, SOC 2, and FINRA impose strict requirements on how client data is stored, transmitted, and logged. Miss a requirement and fines can run into the millions. On the financial side, breach response costs include forensic audits, legal fees, and mandatory notification campaigns that can cost far more than the investment in prevention. Operationally, a compromised communication channel forces teams to halt workflows, rebuild trust, and often replace tooling under crisis conditions.
"A proactive security posture is not simply about checking compliance boxes. It is about protecting the operational continuity of the entire enterprise."
The data reinforces this point. One study found that 69% data reduction was achieved through deduplication and PII (personally identifiable information) redaction across 241,801 instances in a firm processing 13,000 files. That volume of sensitive data moving through a single organization's communication channels shows just how much exposure exists without systematic controls.
Key scenarios where sensitive data is most at risk:
- Unencrypted email threads containing contracts, financial disclosures, or medical records
- File-sharing links with no expiration date or access restriction
- Third-party collaboration apps that store messages on servers outside your data governance policy
- Personal messaging apps used for quick client updates without logging or audit trails
- Departing employees retaining access to client channels beyond their last day
Following security best practices across these scenarios is not optional. Regulators do not accept "we were using standard tools" as a defense when a breach occurs on an unmonitored channel.
Build your security foundation: Essential tools and protocols
Once you understand the risk landscape, the next priority is assembling the right security infrastructure. Attempting to build a secure communication workflow on a weak foundation is like constructing a vault with a screen door. The tools you choose and the protocols you enforce determine whether your process holds under real-world pressure.
End-to-end encryption is the non-negotiable baseline. It ensures that messages and files are scrambled at the sender's device and only decrypted at the recipient's end, meaning no one in between, including the platform provider, can read the content. But encryption alone is not enough.

Here is a breakdown of the essential building blocks for a secure confidential communication environment:
| Security layer | What it does | Minimum standard |
|---|---|---|
| End-to-end encryption | Protects data in transit and at rest | AES-256 or TLS 1.3 |
| Multi-factor authentication (MFA) | Verifies user identity beyond passwords | TOTP or hardware key |
| Role-based access control (RBAC) | Limits who can view or send in each channel | Least privilege model |
| Continuous monitoring | Detects anomalies and unauthorized access in real time | SIEM integration |
| Audit logging | Creates tamper-evident records of all communication events | Immutable log storage |
| Data loss prevention (DLP) | Blocks unauthorized sharing of sensitive content | Policy-driven rules |
The framework that ties these layers together is Zero Trust Architecture. Per NIST SP 800-207, Zero Trust Architecture (ZTA) involves continuous verification of user identity, device health, and context for every access request, regardless of whether the user is inside or outside the corporate network. In distributed enterprise environments where employees work across offices, remote locations, and personal devices, this is not optional. It is the only architecture that accounts for modern threat surfaces.
Pro Tip: Do not deploy Zero Trust as a single product purchase. It is a strategy, not a tool. Map your current identity, device, and network controls to the NIST framework, identify the gaps, and close them systematically. Start with identity verification before tackling device health scoring.
Layered security consistently outperforms relying on any single control. 63% of firms now use two or more vendors for content security across email, messaging, and collaboration tools. Combining encryption with robust access controls and continuous monitoring creates overlapping defenses. If one layer is bypassed, the others catch what slips through. Review the must-have features for secure messaging platforms to assess whether your current stack covers all these bases.
Step-by-step confidential client communication workflow
With a strong security foundation in place, you are ready to implement a repeatable, auditable workflow. The goal here is consistency. A process that only works when someone remembers to follow it is not a process. It is a hope. This is the workflow that turns security controls into daily practice.

Step 1: Authenticate all participants before any exchange Before a single message is sent or a file shared, every participant must complete MFA. This applies to internal team members and any external client access portals. Federated identity, where your system checks the client's authentication against your own before granting access, adds another layer for enterprise-to-enterprise interactions.
Step 2: Assign channel-level access controls Create dedicated, purpose-built channels for each client engagement. Apply RBAC so only the specific team members working on that matter can access that channel. Avoid the common mistake of using a general "clients" channel where multiple engagements overlap. Separation of data at the channel level is a fundamental workflow step that directly reduces exposure.
Step 3: Enforce end-to-end encryption on all file transfers Every document shared within a client channel should be encrypted before it leaves the sender's device. Platforms that handle this automatically at the infrastructure level are far more reliable than processes that depend on users manually encrypting attachments. Verify that the platform's encryption policy extends to files, not just text messages.
Step 4: Log everything and store immutably Audit logging is the memory of your security posture. Configure your platform to log every access event, every message sent, and every file transferred, and store those logs in an environment where they cannot be altered or deleted by any user, including administrators. This is essential for eDiscovery and regulatory audit responses.
Step 5: Run scheduled compliance reviews Designate a recurring review cadence, monthly at minimum, quarterly for lower-risk channels, where IT, compliance, and legal teams jointly review access logs, flag anomalies, and verify that channel membership is current. Team messaging best practices consistently point to scheduled reviews as one of the most effective breach-prevention activities.
Step 6: Apply redaction before any external disclosure Before any communication record is shared outside the platform, whether for a regulatory response, client request, or eDiscovery matter, run it through an automated redaction tool to remove PII and privileged content that is outside the scope of the request. This is where specialized platforms provide a decisive advantage over native tooling.
Step 7: Conduct post-engagement review and archive When a client engagement closes, follow a formal offboarding process. Revoke access for all parties, archive the channel to your secure long-term storage environment, and verify the archive is encrypted and indexed for future retrieval. Do not simply close the channel. Confirm the data is protected.
The payoff for executing this workflow correctly is significant. Enterprises implementing this level of security report 73% fewer security incidents, and that directly translates to reduced legal exposure, better insurance terms, and stronger client retention. For context on how specialized solutions handle these steps in practice, reviewing examples of secure messaging agents and enterprise-grade platforms helps clarify where native tools fall short.
| Workflow step | Native tools (Teams, Slack) | Specialized platforms |
|---|---|---|
| MFA enforcement | Basic | Advanced with device health checks |
| Channel-level RBAC | Limited | Granular, policy-driven |
| Automated redaction | Not available | Built-in |
| Immutable audit logs | Partial | Full, tamper-evident |
| eDiscovery readiness | Requires add-ons | Native |
Pro Tip: Integrate your messaging platform's audit logs directly into your SIEM (security information and event management) system. Real-time alerts for unusual access patterns, like a user downloading an entire channel's file history at 2 a.m., are only possible if your logs feed into a system that can act on them instantly.
Troubleshooting and common mistakes: Keeping communication airtight
Even well-designed workflows break down under pressure. The most common failure points are not technical. They are human and procedural. Knowing what to watch for keeps your process reliable long after the initial rollout.
"Security is not a state you achieve once. It is a practice you maintain continuously, especially as teams change and client engagements evolve."
The mistakes that generate the most damage include:
- Incomplete user training: Team members who do not understand why the process exists will find shortcuts. Regular, role-specific training is non-negotiable.
- Over-reliance on native tools: Native tools like Microsoft Teams handle general collaboration well, but they fall short in eDiscovery and compliance scenarios where specialized platforms can help organizations avoid fines reaching $17.5 million under HIPAA enforcement actions.
- Poor audit log hygiene: Logs that are not regularly reviewed are just data storage costs. Schedule active review, not just passive collection.
- Inconsistent offboarding: Access left active after an engagement closes is an open door. Automate offboarding triggers wherever possible.
- Channel sprawl: When teams create ad-hoc channels outside the formal structure, governance breaks down quickly. Enforce naming conventions and creation policies.
Your enterprise chat security guide should include a monthly audit checklist that covers active user access, encryption policy status, log integrity, and third-party integration permissions. Running your environment against an enterprise messaging security checklist quarterly catches configuration drift before it becomes a breach.
Pro Tip: Assign a named security owner for each client communication channel, not just a team. When accountability is tied to a specific person rather than a group, issues get escalated faster and reviewed more carefully.
Unpacking the reality: What experts get wrong about secure client communications
Here is a perspective most security guides skip: the biggest risk to your confidential communication process is not a sophisticated external attacker. It is the organizational assumption that "good enough" tools and surface-level compliance mean you are protected.
Many enterprises spend considerable energy selecting the right platform, deploying MFA, and writing a security policy. Then they stop. The policy gets documented, the rollout gets celebrated, and the ongoing work of verification, retraining, and auditing quietly deprioritizes as the next initiative takes over. That gap between documented security and practiced security is exactly where breaches live.
The one-size-fits-all mindset compounds this problem. A mid-market professional services firm and a healthcare network face different regulatory environments, different data volumes, and different threat actors. Applying a generic framework without mapping it to your actual client data flows and communication patterns leaves blind spots that attackers, and regulators, will find before you do.
There is also a tendency to treat compliance as the ceiling rather than the floor. Passing an annual SOC 2 audit or meeting HIPAA baseline requirements is the starting point, not the finish line. The layered security approach that 63% of leading firms now use exists precisely because every single layer adds defenses that the others cannot provide alone. Removing a layer to cut costs or simplify operations is a trade-off that rarely looks good in a post-incident review.
The organizations that consistently protect client communications treat security as an operational discipline rather than a project. They audit continuously, train repeatedly, and invest in platforms where encryption is built in by design, not bolted on as an afterthought. That mindset is what separates enterprises that prevent breaches from those that simply respond to them.
Upgrade your confidential client communication process with Luxenger
Executing this level of secure communication workflow requires more than a checklist. It requires a platform built with these requirements at its core, not adapted from a general-purpose tool. Luxenger is designed from the ground up for enterprises where security, auditability, and AI-powered efficiency are not optional features.
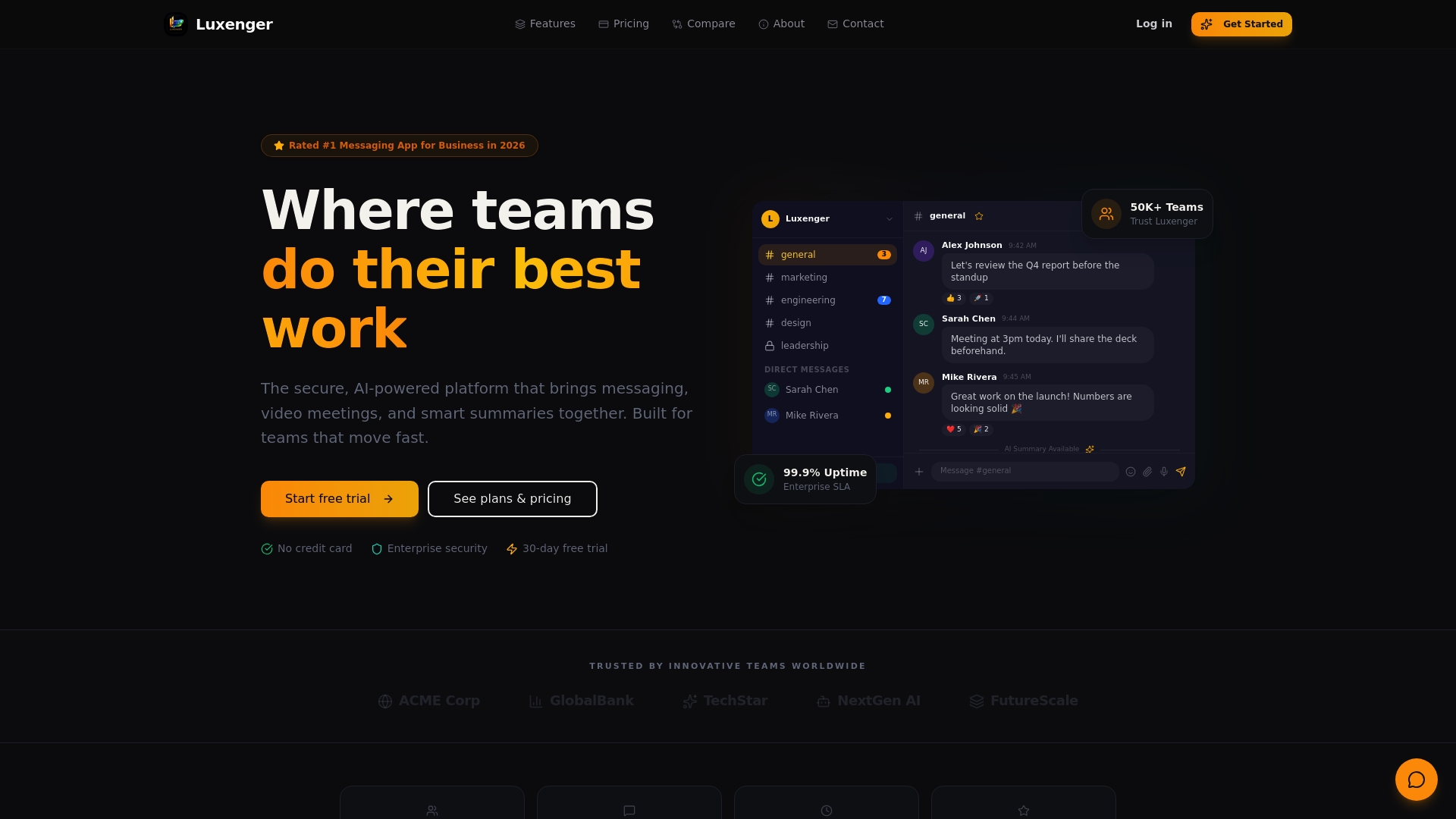
With bank-grade encryption, granular role-based access controls, AI-powered conversation summaries, real-time multilingual translation, and voice huddle capabilities, Luxenger gives IT and communications teams the infrastructure to handle even the most sensitive client interactions with confidence. Whether you are managing a global financial services firm, a healthcare network, or a legal practice, the platform scales to your compliance requirements. Explore the full capability set on the enterprise messaging platform page, or review Luxenger pricing to find the right fit for your organization's size and security needs.
Frequently asked questions
What is the most important step in securing client communications?
Continuous verification using a Zero Trust approach is the single most important step, as NIST SP 800-207 recommends validating user identity, device health, and context at every access request without exception.
How do specialized messaging platforms improve compliance?
Specialized platforms provide built-in audit logging, automated redaction, and eDiscovery capabilities that native tools lack, helping organizations avoid regulatory penalties that can reach $17.5 million under HIPAA enforcement actions.
Are layered security measures really necessary?
Yes, because no single control catches every threat. Firms that implement layered security combining encryption, access controls, and monitoring report dramatically fewer incidents and significantly lower insurance premiums compared to single-measure approaches.
What is the typical ROI from a secure client communication process?
Beyond breach avoidance, organizations consistently report 18 to 22% reductions in insurance premiums when enterprise-grade security is implemented, alongside measurable improvements in audit readiness and client retention.
